What is CVSS and why do you need it?
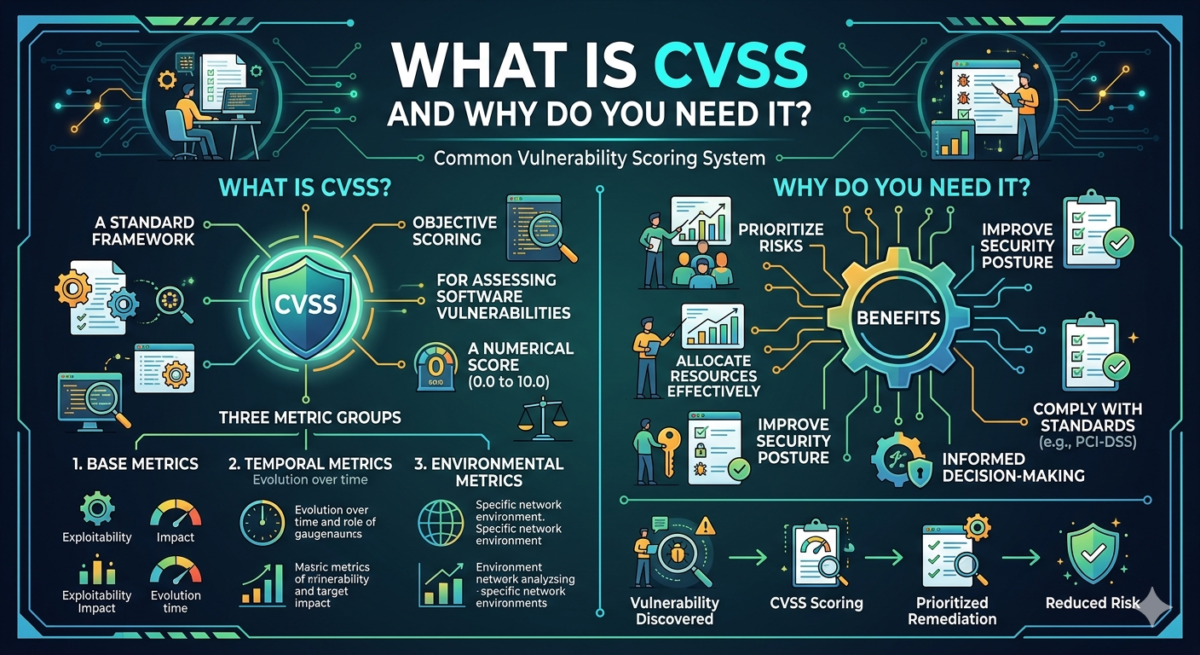
CVSS is an open standard that describes software vulnerabilities and assigns a numerical score on a scale of 1 to 10: the higher the score, the more serious the potential cybersecurity impact.
Table of Contents
If you work for a company with an internal network, internet access, a server rack, or cloud storage, knowing CVSS will definitely come in handy. Every day, experts identify dozens of new vulnerabilities in software, hardware, or cloud platforms. But which ones are truly dangerous, and which don’t pose a serious threat? To find out, the Common Vulnerability Scoring System (CVSS) exists. Read on to learn:
- Who developed this system?
- How can it be used in practice?
- What metrics are included in the standard?
- What you need to know about vulnerabilities if you don’t work in information security
- Why should businesses use CVSS?
What is CVSS in simple terms?
It’s important to emphasize: CVSS doesn’t evaluate the severity of a vulnerability per se, but rather its severity —this is only part of the overall risk analysis. Let’s imagine a sensitive security flaw with a critical score is discovered in a system. At first glance, it seems urgent to fix. However, a vulnerability may be discovered in a component that isn’t used at all in the infrastructure. For example, the services the component relies on are disabled at the network level. An attack on them is only possible under certain configurations. Bottom line: the actual danger from the vulnerability is almost zero, despite its high score.
CVSS shows how “bad” a vulnerability might be in a vacuum. But how “dangerous” it is for your project is a matter of risk analysis, which qualified information security specialists can help with.
Therefore, it is important not to confuse the concepts and to use CVSS as a tool, not as the sole criterion for assessing threats.
The assessment is based on a set of formulas and metrics that can be divided into several categories:
Baseline vulnerabilities are vulnerabilities in their original state, without taking time factors into account.
Temporal vulnerabilities are vulnerabilities that take time, exploit availability, and mitigation measures into account.
Impact vulnerabilities are vulnerabilities that take into account the context of system use, its impact on business, and other factors.

Professionals can use publicly available vulnerability calculators to identify, assess, and prioritize risks: the NIST calculator.
Who invented the CVSS system?
The system was developed by a team of specialists from the world’s largest corporations, such as Cisco, Microsoft, and others. The standard is supported and developed by the security working group of the Forum of Incident Response and Security Teams (FIRST).
The first version of CVSS was released in 2005. The latest version to date is version 4.0, which was released in 2024.
Besides CVSS, there are other vulnerability assessment methodologies and lists. For example, OWASP (in the context of web application risk assessment) or CVE, a database of known vulnerabilities used as a data source for CVSS assessments.
Who uses CVSS in practice?
CVSS is used not only by information security specialists, but also by other participants in the IT ecosystem:
1. Software vendors
Software developers and vendors use CVSS to classify vulnerabilities found in their products.
For example, Microsoft assigns a CVSS score to each vulnerability it finds and publishes this information in security bulletins. This helps users assess the risks and decide how urgently they need an update.
2. CVSS helps information security teams
Prioritize vulnerability responses.
For example, if a vulnerability scanner finds dozens of issues, CVSS scores can help quickly filter out low-priority ones and focus on critical threats (e.g., those with a score above 9).
3. DevOps and SRE teams
: For teams responsible for service and infrastructure operations, CVSS helps decide which updates to install first and how to automate patch installation.
Vulnerability management systems can be configured to automatically update libraries or containers if vulnerabilities with a high CVSS score are found in them.
4. Cloud Platforms
If you work with services like GitHub, Docker, AWS, Google Cloud, or use Linux distributions, CVSS already impacts your experience:
- GitHub automatically analyzes project dependencies and displays vulnerability warnings with CVSS scores.
- Docker marks insecure images based on the presence of vulnerabilities with a high CVSS.
- Cloud providers issue updates and recommendations based on this assessment.
CVSS influences update priority—major software vendors (e.g., Microsoft, Cisco, Adobe) prioritize patch releases based on CVSS scores. Vulnerabilities with a score above 7.0 are typically given critical priority for fixing.
Even if you don’t use CVSS directly, it impacts the software ecosystem, updates, and security that you interact with every day.
If you are a business owner and you don’t have an information security education, but it is useful for you to know this
Here are a few tips to get you up to speed and help you navigate the context of information security and CVSS.
- Look at the numbers —for example, CVSS 7+ means that updating shouldn’t be delayed, but CVSS 9+ is a serious risk, especially if an exploit is already available.
- Remember that not all CVSS scores are created equal. Context is key—if a vulnerability was found in a component you don’t use, you can breathe a sigh of relief.
- Don’t neglect automation. Modern scanners and monitoring systems can take CVSS into account, and then the key is to respond appropriately to detected threats.
- The safety of your business will depend largely on information security. Unfortunately, such is the reality of the modern world, where damage from hackers can amount to millions of rubles.
- Try to independently study cybersecurity trends and read news on this topic. A simple rule applies here: “forewarned is forearmed.”
CVSS is of interest not only to security specialists but also to attackers themselves, who are constantly searching for new hacking methods and improving their skills. Hackers monitor vulnerability ratings and often add the highest-scoring (CVSS) vulnerabilities to their automated hacking tools.
CVSS Ranges and What They Mean for Your Security
To understand how to interpret CVSS numeric values and what they mean in practice, consider a table with risk levels and example vulnerabilities:
|
CVSS range |
Risk level |
What does it mean? |
Examples of real vulnerabilities |
|
0 |
no risk |
does not pose a threat |
CVE-2017-14940 (Logical Error Without Consequences) |
|
1-4 |
short |
exploitation is unlikely, or the effect is minimal |
CVE-2020-25692 (Fedora Unstable Component) |
|
4-7 |
average |
The vulnerability can be exploited |
CVE-2022-30190 (Follina, before widespread exploitation) |
|
7-9 |
high |
A remote attack is possible; data can be compromised |
CVE-2021-44228 (Log4Shell) – Early Stage |
|
9-10 |
critical |
easy exploitation of a vulnerability and still causing serious damage, often via remote code without physical access or an account |
CVE-2021-44228 (Log4Shell), CVE-2017-0144 (EternalBlue) |
Trending vulnerabilities of 2025 from the NIST
WindowsThe
database Vulnerabilities with identifiers CVE-2024-38014 and CVE-2024-38217 allow attackers to locally escalate their privileges to the SYSTEM level, bypassing the Mark-of-the-Web protection mechanism, and then disguise malicious objects as legitimate files.
Veeam Backup & Replication
vulnerability CVE-2024-40711 allows unauthorized users to remotely execute arbitrary code, which can compromise the server and disrupt the entire IT infrastructure.
VMware vCenter
vulnerability CVE-2024-38812 allows remote code execution without authorization. This allows attackers to gain complete control over the virtualization management system.
Web Applications
Vulnerabilities CVE-2024-37383 in Roundcube Webmail and CVE-2024-8275 in The Events Calendar plugin (for WordPress) allow attackers to inject JavaScript code to gain database access and compromise user accounts.
Conclusion: Why do businesses and IT teams need this?
Using CVSS is important not only for technical specialists but also for businesses as a whole. Assessing the severity of vulnerabilities helps prioritize updates, fix vulnerabilities before they can be exploited, and reduce the risk of downtime, data breaches, and fines for non-compliance with security requirements.
If you’re a manager, implementing CVSS will help you make informed decisions about cybersecurity investments and risk management. Automated vulnerability-based scanners improve the maturity of information security processes and reduce incident response times.