Category: Cybersecurity
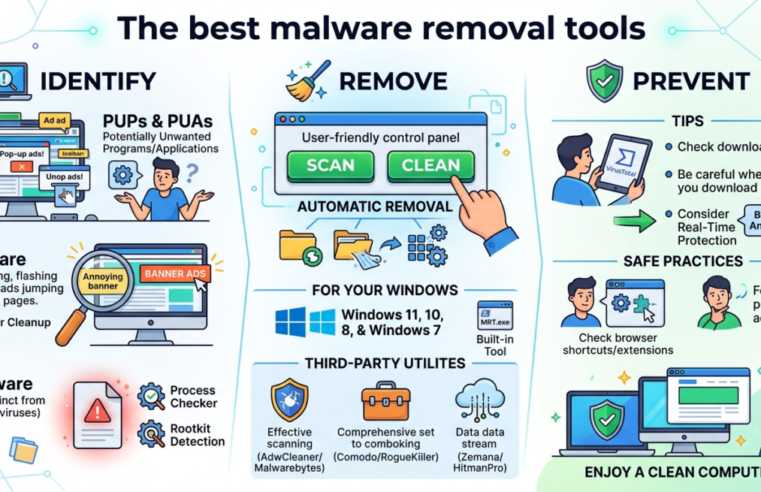
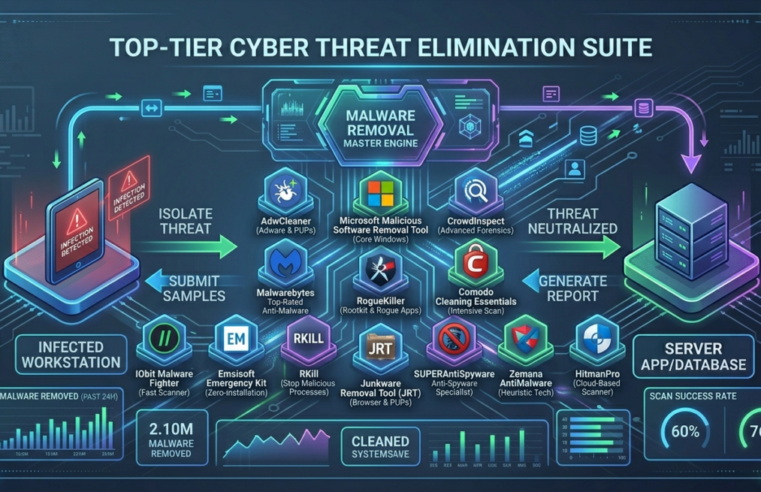
The best malware removal tools
Malware, as defined in this article (PUP, AdWare, and Malware), is not exactly a virus, but rather programs that exhibit unwanted activity on a computer (advertising windows, incomprehensible computer and browser
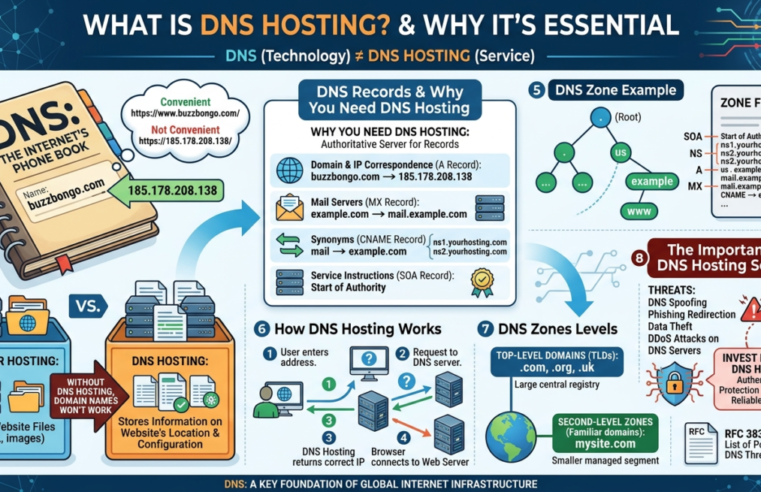
Read MoreWhat is DNS hosting?
DNS hosting is a large topic within another, even larger topic: DNS. This article explains in more detail why it’s important to ensure DNS hosting security, who needs it, and
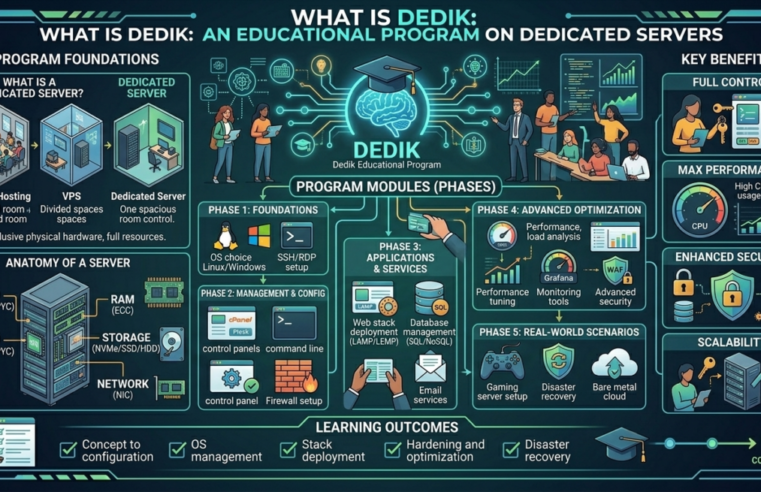
Read MoreWhat is Dedik: An educational program on dedicated servers
High-load projects require dedicated solutions. Why dedicated servers are the ideal choice for high-traffic sites with unique requirements. What is a Dedicated Server? A Dedicated Server is a dedicated physical
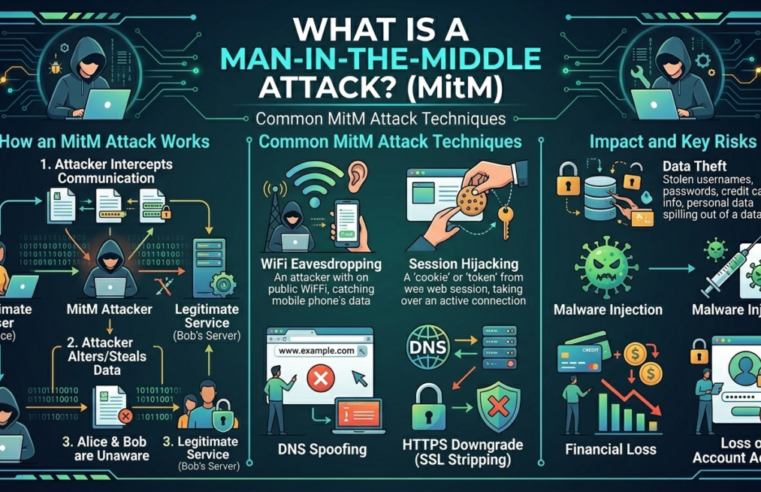
Read MoreWhat is a Man-in-the-Middle attack?
In this article, we’ll explore why it’s important to protect your resources from a relatively old, but still relevant, cryptographic attack—the “man-in-the-middle” (MitM). To better understand the mechanics of a
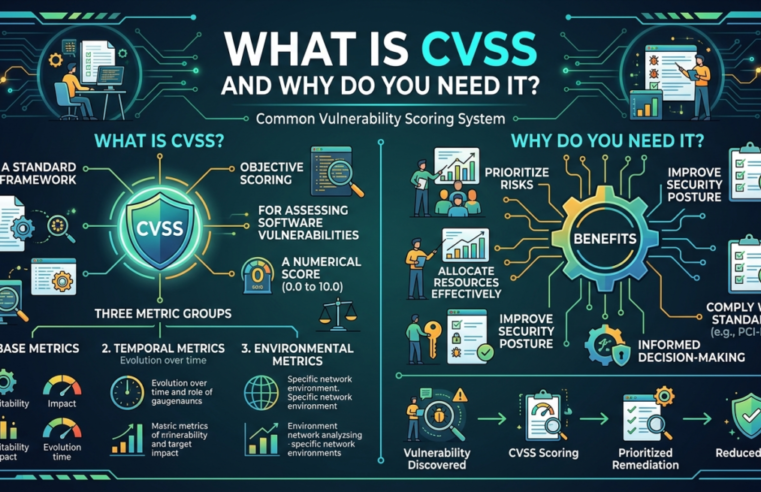
Read MoreWhat is CVSS and why do you need it?
CVSS is an open standard that describes software vulnerabilities and assigns a numerical score on a scale of 1 to 10: the higher the score, the more serious the potential cybersecurity
Read MoreSocial engineering in information and cybersecurity
Human-based attacks (social engineering) remain the most popular method of cyberattacks against both organizations (50%) and individuals (91%, according to penetration testing data for Q1 2023). Phishing emails and web
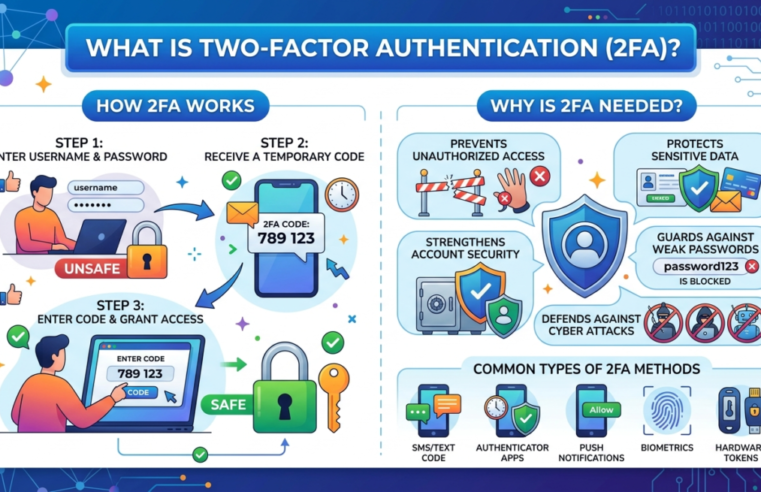
Read MoreWhat is two-factor authentication (2FA) and why is it needed?
Two-factor authentication is essential for the security of personal data and accounts. In this article, we’ll explore how it works, the types of second factors, and share recommendations for using
Read MoreCybersecurity in the Age of Artificial Intelligence
In an era of rapid technological advancement, artificial intelligence is becoming an integral part of our daily lives. Its applications span a wide range of fields, from medicine and finance
Read MoreThe Importance of Cybersecurity
Understand why cybersecurity is important and the different types of threats it can protect you from. Just as you protect your home by locking the door when you leave, you
Read MoreThe best malware removal tools
Malware, as defined in this article (PUP, AdWare, and Malware), is not exactly a virus, but rather programs that exhibit unwanted activity on a computer (advertising windows, incomprehensible computer and
Read More