What is a Man-in-the-Middle attack?
In this article, we’ll explore why it’s important to protect your resources from a relatively old, but still relevant, cryptographic attack—the “man-in-the-middle” (MitM).
Table of Contents
To better understand the mechanics of a man-in-the-middle (MitM) attack, let’s start with the basic principles of symmetric encryption using the DES algorithm as an example. This algorithm was developed in the 1970s at IBM and is considered one of the starting points for the development of modern practical cryptography.
DES encrypts data by breaking the original message into fixed-size blocks of 64 bits. Each block is processed sequentially in 16 rounds, during which bits are permuted using a secret key. Decryption follows the same principles, but in reverse order of the rounds.

This simplified description does not cover all the cryptographic details of the algorithm, but it is sufficient for a general understanding of how a block cipher works.
It’s important to emphasize that the DES algorithm is now considered cryptographically obsolete. Its length is too short, and modern computing power allows brute-force attacks to be performed in a relatively short time. For this reason, DES is rarely used in modern system security solutions.
It has been replaced by new algorithms, such as AES, which have significantly higher cryptographic strength and are used in most current data protection protocols.
Man-in-the-Middle (MitM) attack
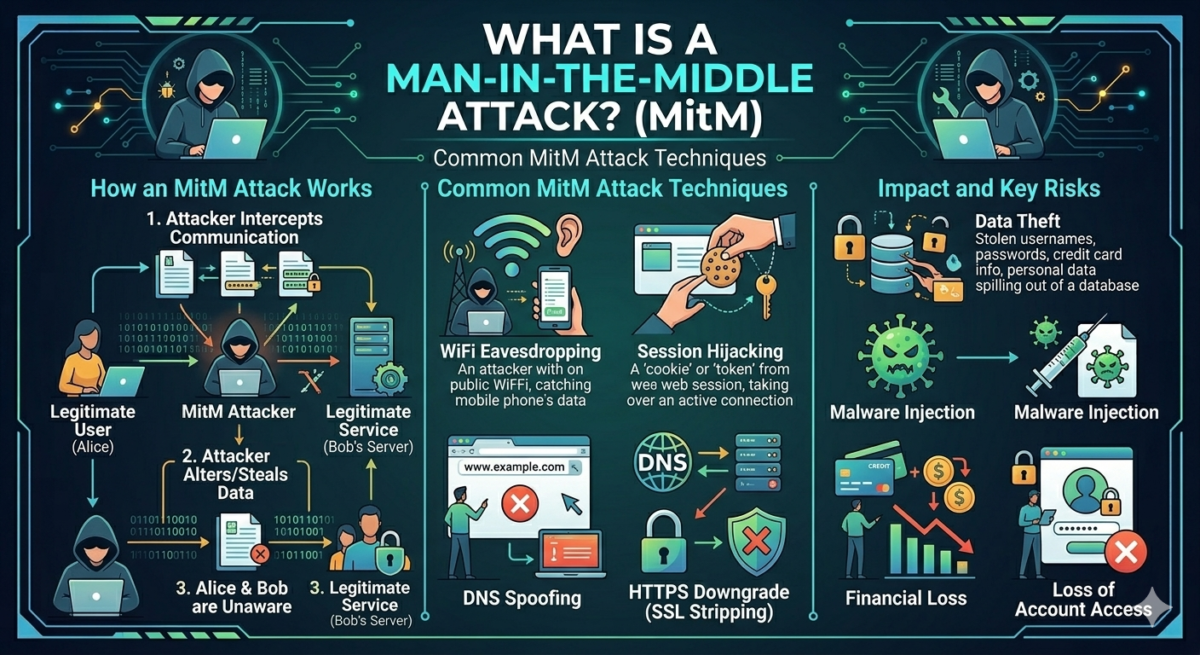
The name of a MitM (man-in-the-middle) attack suggests its basic principle: introducing a third party into the data exchange between two communicating parties. As a result, the attacker, unbeknownst to the victim, intercepts and relays messages between, for example, the infamous Alice and Bob, each of whom believes they are communicating directly with the other.
The key feature of a MitM attack is that the attacker effectively establishes two separate connections: one with Alice and one with Bob. The attacker can act as “Alice” to Bob and as “Bob” to Alice. Depending on the attack’s objectives, they can limit themselves to passively intercepting traffic or actively modify transmitted data: altering message content, spoofing commands, deleting or inserting new data.
MitM attacks are especially dangerous when the parties fail to properly authenticate each other. Typical technical scenarios for MitM implementation include TLS certificate spoofing, attacks on key exchange protocols, ARP spoofing on local networks, DNS spoofing, and the use of fake Wi-Fi access points. Even with modern cryptographic algorithms, an attack can be successful if authentication and trust mechanisms are compromised.
What does encryption have to do with the DES algorithm?
We began this article by explaining the basic DES encryption algorithm, which is used by the sender and receiver to establish a secure communication channel. DES requires both Alice and Bob to know the same secret decryption key. If this key is transmitted over an unsecured channel, a vulnerability arises:
- Alice and Bob want to use DES to encrypt their communication.
- Ivan sends Dmitry a secret DES key.
- The attacker intercepts this exchange and:
- or learns the common key;
- or substitutes keys by sending different keys to Alice and Bob.
Result:
- Alice encrypts messages with one key (which is known to the attacker);
- Bob – with another key (also known to the attacker);
- The attacker is free to decrypt, read, and re-encrypt messages between the two parties.
However, the encryption algorithm itself is not considered hacked, since it operates strictly according to the specifications that the attacker uses for his own purposes.
DES was developed in an era when secure key exchange over open networks was either unsafe or largely unimportant. It has no built-in authentication mechanisms and relies entirely on an external key transmission channel.
Which protocols are vulnerable to man-in-the-middle attacks?
First of all, a MitM attack is possible not because of weaknesses in the cryptographic algorithms themselves, but because of vulnerabilities in data transfer protocols, authentication mechanisms, and trust management. Below, we will consider the main classes of protocols that, due to their historical architecture, are susceptible to MitM attacks.
1. Insecure application protocols
Protocols that do not provide encryption and authentication are inherently vulnerable to MitM, since all traffic is transmitted in cleartext:
- HTTP – transfers web page data
- FTP is one of the basic data transfer protocols
- SMTP, IMAP (without TLS) – provides data transfer between mail servers
In such protocols, a MitM attack does not require the attacker to know complex techniques: it is sufficient to gain access to the network segment through which the traffic passes.
2. Protocols with optional or incorrectly configured encryption
Some protocols support secure modes of operation but allow insecure configurations:
- HTTP/ HTTPS without redirect
- SMTP with the STARTTLS extension (allows you to create an encrypted connection on top of the main protocol)
- IMAP/POP3 with STARTTLS extension (as in the previous example)
By exploiting protocol specifics, an attacker can block or spoof attempts to switch to an encrypted connection. The client and server will then continue to operate in unencrypted mode, unaware of the attack.
3. Network protocols without built-in security
At the creation stage, the basic network protocols were designed without taking into account modern threats and are therefore easily susceptible to substitution.
- ARP (Address Resolution Protocol)
- does not have authentication mechanisms
- allows an attacker to spoof MAC addresses
- widely used for MitM in local networks (ARP spoofing)
- DNS
- Classic DNS does not check the authenticity of responses
- allows for IP address substitution (DNS spoofing)
- used to redirect victims to fake resources
4. Wi-Fi protocols and wireless connections
Wireless environments are particularly vulnerable due to the open nature of data transmission:
- open Wi-Fi networks
- obsolete standards such as WEP or WPA
An attacker can spoof access points or force clients to reconnect, as well as intercept traffic.
5. Secure protocols with implementation errors
Incorrectly configured protocols leave vulnerabilities that create risks for attacks:
- TLS without certificate chain verification
- acceptance of self-signed certificates
- No HSTS (HSTS headers are recommended for use on all pages to indicate to the browser that it should always request pages via HTTPS rather than HTTP, as HTTPS uses secure encryption)
Main MitM attack scenarios
Key substitution in asymmetric systems
In public-key encryption infrastructures, an attacker can intercept and replace public keys during the connection establishment phase. This allows them to become an intermediary between two encrypted channels and gain the ability to read and modify transmitted data. Digital certificates and public-key infrastructure are used to protect against such attacks.
Interference with transmitted data
In a MitM position, an attacker can not only intercept traffic but also actively modify it, allowing them to hijack authorized sessions, execute commands on behalf of the user, and inject malicious code into web pages and downloaded files.
Downgrade attacks
An attacker can force a connection to switch to outdated or less secure protocols and algorithms that are retained for compatibility. Such attacks are possible in SSH, IPsec, and PPTP if insecure modes remain active.
Exploitation of obsolete protocols
Examples include forcing the use of SSH-1 instead of SSH-2, running IPsec in fallback mode without encryption, and choosing weak authentication methods in PPTP. All of these scenarios allow an attacker to access data without breaking the cryptography.
Public communication platforms
In messaging services, email, and social media, the platform operator technically controls the communication channel. In such cases, a MitM attack relies not on technical vulnerabilities, but on users’ trust in the intermediary and their disregard for information security requirements.
How to detect an attack
Detecting a MitM attack is typically quite difficult, even for an experienced specialist. However, several signs indicate malicious activity by a third party:
- security warnings about certificates or encryption when accessing a secure site
- A slow internet connection may indicate that your data is being routed through an attacker’s server.
- If you find yourself logged out of all your accounts for no apparent reason
- The appearance of unknown devices on your corporate or home network
- Unknown or new extensions have appeared in the browser
Ways to protect against MitM attacks
Use secure data transfer protocols.
Any network communication should be carried out exclusively over encrypted communication channels. Using HTTPS with properly configured TLS mechanisms will prevent data interception and spoofing by encrypting data during transmission.
Verifying the Authentication of Parties Using PKI Technology
With PKI, digital certificates and a public key infrastructure (PKI) are used to verify the identity of the parties before establishing a connection. These can detect attempts to spoof the server or infiltrate the data exchange process.
Using virtual private networks
A VPN creates a secure tunnel over a public network, hiding transmitted data from prying eyes.
Network security tools
Modern antivirus solutions and firewalls can detect anomalies in network traffic, attempts to inject malicious certificates, and other signs of MitM attacks. Proper configuration reduces the risk of successful exploitation of vulnerabilities.
MitM testing scenarios
Using tools like Ettercap, you can simulate attackers’ actions during a MitM attack in a secure testing environment. During testing, specialists will identify potential vulnerabilities in DNS, TLS, Wi-Fi, and other internal services, which should then be patched as quickly as possible.
Regular software updates
Outdated versions of operating systems and applications often contain known vulnerabilities that are actively exploited in MitM attacks. Software updates, while basic, are critical.
Digital hygiene
Phishing emails are often the first stage of MitM attacks, including link and certificate spoofing. Train your employees so they know how to react when receiving suspicious messages.
Using the HSTS protocol
HSTS forcibly disables unsecured connections and prevents SSL stripping attacks, reducing the risk of users undetected switching to unsecured communication channels.
The principle of least privilege
Dividing the network infrastructure into isolated zones and restricting access between them reduces the potential attack surface. If a MitM attack is successfully implemented, an attacker will not be able to access all of the organization’s traffic.
Network traffic analysis
IDS/IPS and SIEM systems can detect signs of an attack based on anomalies in network connection behavior, unexpected certificate changes, or unusual traffic patterns.
Use professional traffic analysis systems to detect vulnerabilities. This will prevent malicious actions from occurring, rather than dealing with their critical consequences.
MitM attacks are one of the most dangerous and difficult-to-detect threats—long-term, systematic actions by attackers aimed at undetected interception and eavesdropping on traffic. A successful attack will result in the usual and highly undesirable consequences for any business: compromised credentials, financial losses, leaks of personal and commercial information, and erosion of trust in digital services.
MitM protection should be considered a mandatory element of the basic information security architecture, not an additional measure, and should include a combination of network monitoring and proper protocol configuration.