A major flaw in cPanel was widely used in the “Sorry” ransomware attack.

The newly disclosed cPanel flaw tracked as CVE-2026-41940 is being widely exploited to break websites and encrypt data in the “Sorry” ransomware attack.
This week, an emergency update for WHM and cPanel was released to fix a critical authentication bypass bug that allows attackers to access control panels.
WHM and cPanel are Linux-based web hosting control panels for server management and website administration. While WHM provides server-level control, cPanel provides administrator access to the website’s backend, webmail, and database.
Shortly after its release, it was reported that the flaw was widely used in the wild as a zero-day, with exploit attempts beginning in late February.
Internet security watchdog Shadowserver now reports that at least 44,000 IP addresses using cPanel are vulnerable to an ongoing attack.
The cPanel flaw was exploited in the Sorry ransomware attack
Multiple sources told BleepingComputer that hackers have been exploiting a cPanel flaw since Thursday to breach servers and release the Go-based Linux encryptor for the “Sorry” ransomware. [VirusTotal].
There have been many reports of websites affected by the attack, including the BleepingComputer forums, where the victim shared samples of encrypted files and the contents of a ransom note.
Since then, widespread exploitation and ransomware attacks have been observed, with hundreds of compromised sites already identified on Google.
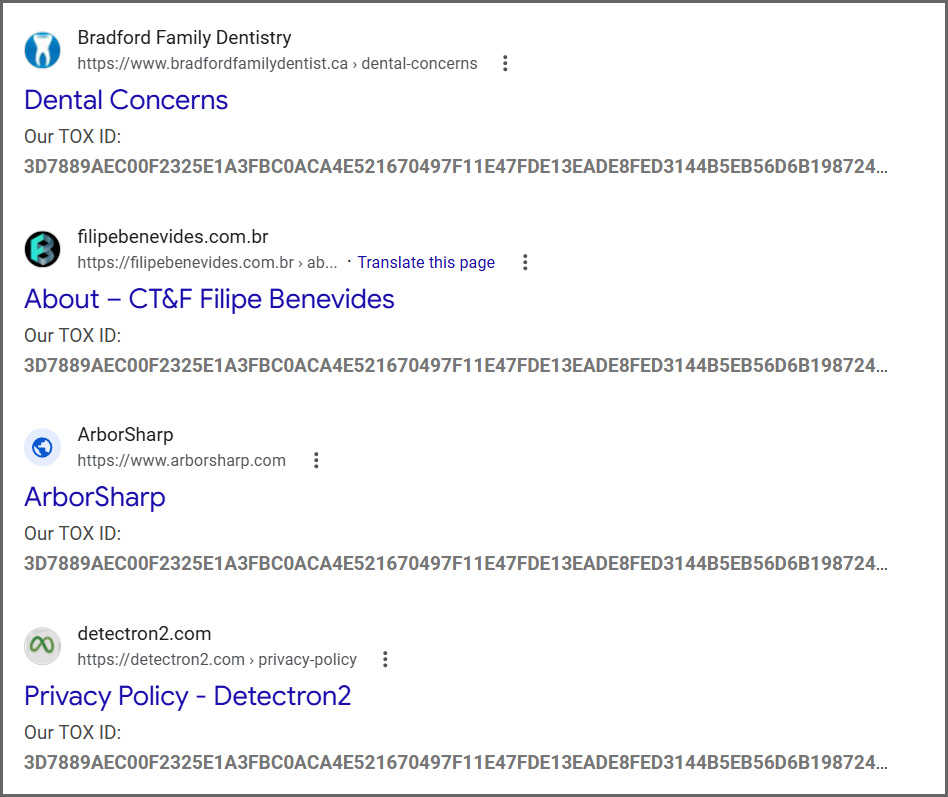
Source: BleepingComputer
Sorry ransomware encryptor is designed specifically for Linux and will include “.I’m sorry” extension to all encrypted files.
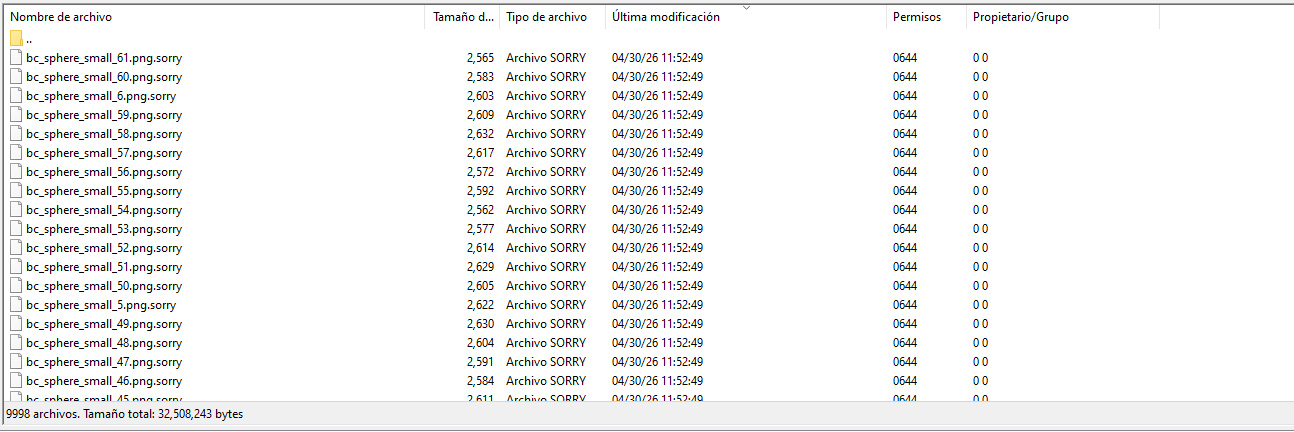
Source: diozada at BleepingComputer forums
BleepingComputer was told that the ransomware uses the ChaCha20 stream cipher to encrypt files, with the encryption key protected using an embedded RSA-2048 public key.
Ransomware expert Rivitna says the only way to decrypt these files is to find the corresponding RSA-2048 private key.
“Decryption is not possible without RSA-2048 private key,” Rivitna posted on our forums.
In each folder, a named ransom note README.md is created, instructing the victim to contact the threat actor on Tox to negotiate a ransom payment.
The ransom note is the same for each victim of this ransomware campaign, including the Tox ID “3D7889AEC00F2325E1A3FBC0ACA4E521670497F11E47FDE13EADE8FED3144B5EB56D6B198724,” which is used to communicate with the threat.
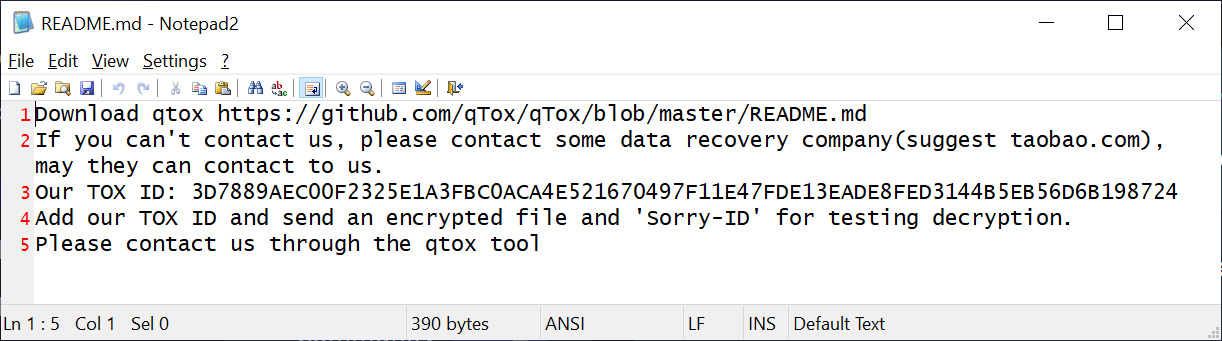
Source: BleepingComputer
It should be noted that a 2018 ransomware campaign used the HiddenTear encryptor to encrypt the files and added the .sorry extension. This current campaign uses a different encryptor and is unrelated.
All cPanel and WHM users are urged to immediately install available security updates to protect their websites from ransomware attacks and data theft.
The attacks are just beginning, and we will likely see more exploits in the coming days and weeks.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



