DAEMON Tools has been used in supply chain attacks for backend use

Cybercriminals compromised DAEMON Tools software installers and since April 8th, introduced a backdoor to thousands of systems that downloaded the product from the official website.
Supply chain attacks have led to thousands of infections in more than 100 countries. However, the loading of the second stage was installed only on twelve machines, indicating a targeted attack aimed at a high-value target.
Among the victims receiving the next-level downloads are commercial, scientific, government, and manufacturing organizations in Russia, Belarus, and Thailand.
A report today from the cybersecurity company Kaspersky notes that the attack continues and that the trojanized software includes DAEMON Tools versions from 12.5.0.2421 to 12.5.0.2434, specifically DTHlper.exe, DiscSoftBusServiceLite.exe, and DTSHellriesHlp.
DAEMON Tools is a Windows utility that allows mounting disk image files as virtual drives. The software was very popular in the 2000s, especially among gamers and power users, but today its deployment is limited to areas where virtual drive management is required.
As of today, Kaspersky says the attack is ongoing.
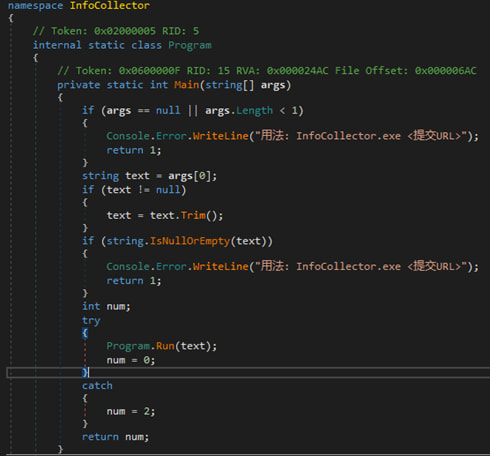
When unsuspecting users download and use digitally signed installers, they trigger malicious code embedded in corrupted binaries. The payload establishes persistence and activates the backdoor at system startup.
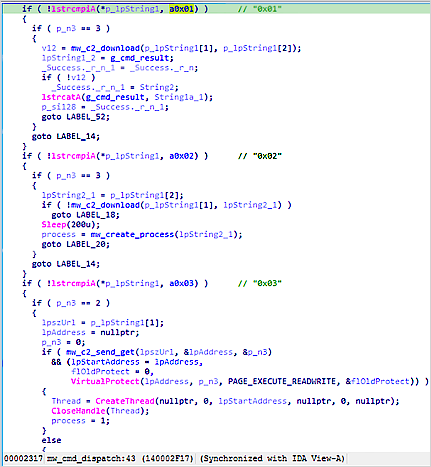
The server can respond with commands instructing the system to download and apply additional payloads.
First-stage malware is basic information theft that collects system data, such as hostname, MAC address, running processes, installed software, and system location, and sends it to attackers to profile the victim.
Source: Kaspersky
Based on the results, some systems get a second tier, which is a lightweight backdoor that can execute commands, download files, and execute code directly in memory.
Source: Kaspersky
In at least one case targeting a Russian academic institution, Kaspersky has seen the deployment of a more advanced form of malware called QUIC RAT, which supports multiple communication protocols and can inject malicious code into legitimate processes.
BleepingComputer contacted DAEMON Tools for comment on the supply chain attack, but has not heard back from publication.
Kaspersky describes the DAEMON Tools-chain attack as a sufficiently sophisticated compromise that it avoided detection for almost one month.
“Given the seriousness of the attack, it is important for organizations to carefully check machines that had DAEMON Tools installed, for unusual cybersecurity-related activities that occurred on or after April 8,” the researchers said.
Although Kaspersky did not attribute the attack to a specific threat actor, based on the strings found in the first-stage payload, researchers believe the attacker speaks Chinese.
Since the beginning of the year, software-supply chain attacks have been detected almost every month: eScan in January, Notepad++ in February, CPU-Z in April, and DAEMON tools this month.
Similar attacks targeting code repositories, packages, and extensions have become more common this year, with the Trivy, Checkmarx, and Glassworm campaigns among the most prominent.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



