The Zara data breach exposed the personal information of 197,000 people

Hackers who accessed the database of Spanish fast fashion retailer Zara stole the data of more than 197,000 customers, according to data breach notification service Have I Been Pwned.
Zara has more than 1,500 company-owned and franchised stores worldwide and is the flagship brand of the Inditex Group, one of the world’s largest fashion distribution groups, which also owns Bershka, Zara Home, Oysho, Pull&Bear, Massimo Dutti, Stradivarius, and Uterqüe.
As Inditex said last month, when the data breach was widely reported, the compromised database was hosted by a former technology provider and contained information about business relationships with customers in various markets.
However, Inditex noted that the attackers were unable to access affected customers’ names, phone numbers, addresses, credentials, or payment information (such as bank cards).
It also added that its operations and systems were not affected, but it has yet to disclose the breach of a specific threat actor and share the name of the hacked provider.
“Inditex has immediately implemented its security measures and has begun to notify the relevant authorities of this unauthorized access, which stems from a security incident that affected a former technology provider and affected several companies operating around the world,” Inditex said.
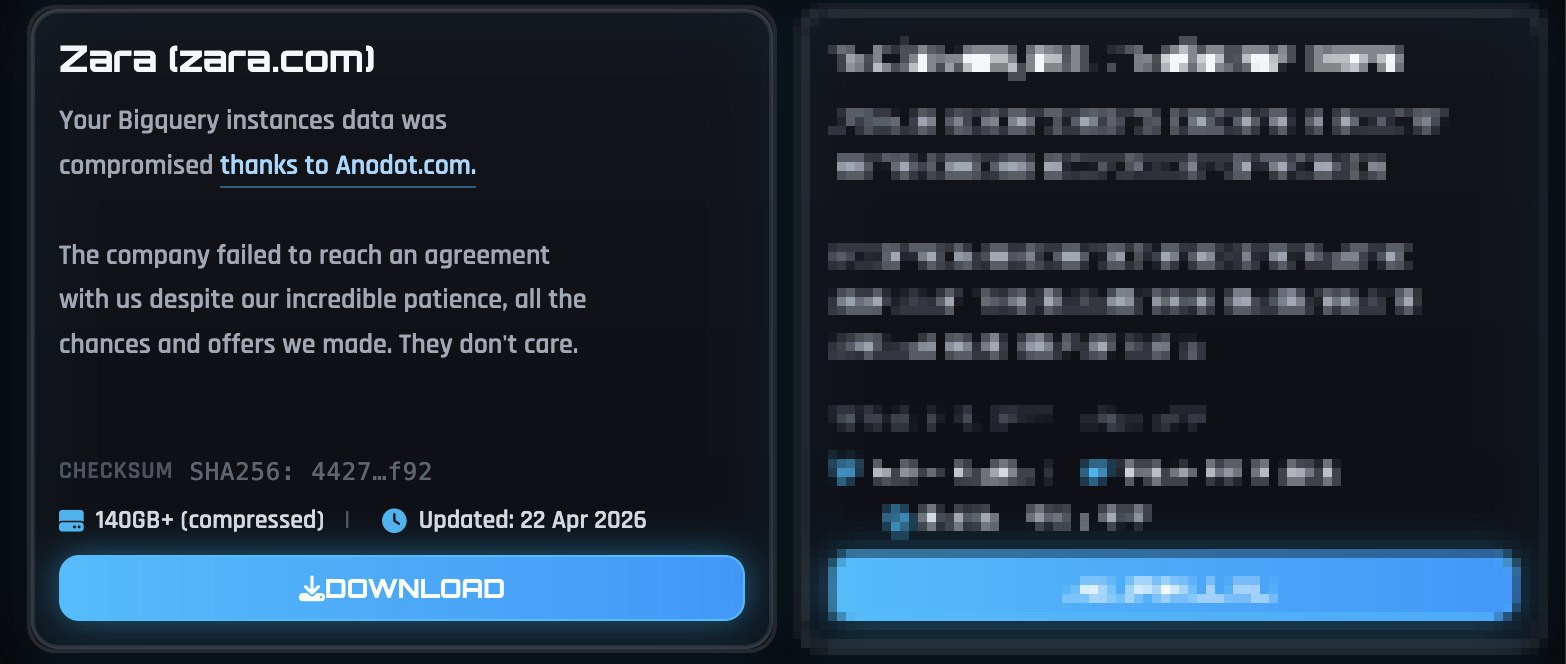
While Inditex and Zara have yet to reveal more details about the incident, including the total number of people affected, the ShinyHunters gang has since claimed responsibility for the breach and leaked a 140GB archive containing documents allegedly stolen from BigQuery instances using vulnerable Anodot authentication tokens.
Have I Been Pwned analyzed the stolen data and said today that the resulting data breach exposed 197,400 people’s data, including unique email addresses, geographic locations, purchases, and support tickets. “The data contains 197k unique email addresses alongside product SKUs, order IDs and the market the support ticket originated from,” says Have I Been Pwned.
Previously, the cybercriminal gang told BleepingComputer that it had stolen data from several companies using Anodot’s authentication tokens, adding that it was blocked by AI-based detection when it tried to steal data from Salesforce instances.
The group was also linked to a widespread phishing campaign targeting employees and Business Process Outsourcing (BPO) accounts of Microsoft Entra, Okta, and Google SSO accounts to steal data for connected SaaS applications (including Salesforce, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, Microsoft Brespace account, Google corporate SSO, SSO 365, and others)
Other breaches reported by ShinyHunters in recent months include Google, Cisco, PornHub, online dating site Match Group, video service Vimeo, Rockstar Games, home security firm ADT, the European Commission, cloud development platform Vercel, edtech giant McGraw Hill, medical device maker Medtronic, cruise line operator Carnival, online training company of Univendemy.
Recently, ShinyHunters hacked education technology giant Instructure twice, the second time using security vulnerabilities to take down the Canvas admissions portals of nearly 330 colleges and universities and threatening to leak data stolen from previous breaches unless a ransom was paid.
MANGO, another Spanish fashion retailer giant, also sent data breach notices to its customers in October, warning them that personal data used in marketing campaigns had been compromised after its retailer was hacked. However, no ransomware or extortion groups have claimed the MANGO incident, so the attackers are still unknown.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



