TrickMo Android bank accepts TON blockchain for covert comms
.jpg)
The new variant of the TrickMo Android banking malware, delivered in campaigns targeting users across Europe, introduces new commands and uses the Open Network (TON) for communication and control manipulation.
TrickMo Bank was first seen in September 2019 and continues to evolve, receiving regular updates since then.
By October 2024, Zimperium analyzed 40 types of malware delivered by 16 droppers, communicating with 22 different command and control (C2) infrastructures, and targeting sensitive user data worldwide.
The latest variant was discovered by ThreatFabric, tracking it as ‘Trickmo.C’. Researchers have been watching this version since January.
In today’s report, ThreatFabric says the malware is disguised as TikTok or streaming apps and targets the bank and cryptocurrency wallets of users in France, Italy and Austria.
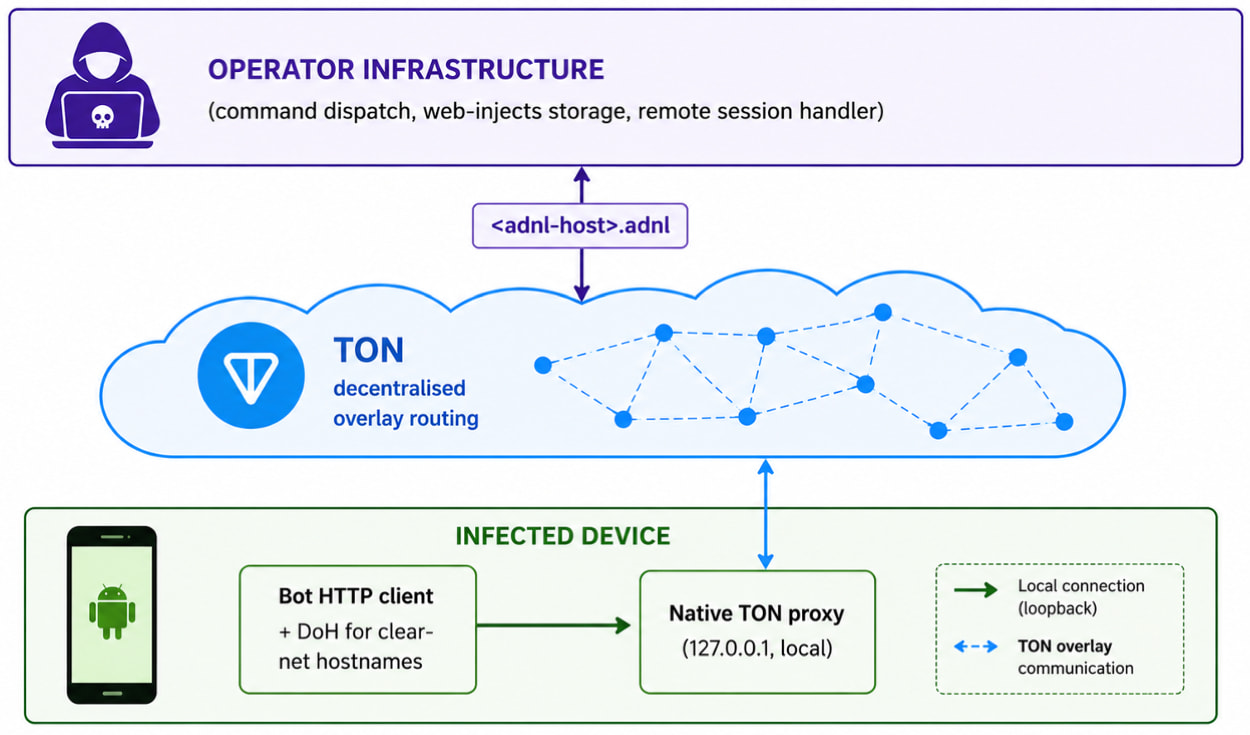
The main new feature of the current variant is TON-based communication with the user, which uses .ADNL addresses routed through an embedded local TON proxy running on the infected device.
TON is a peer-to-peer network originally built around the Telegram ecosystem that allows devices to connect to the web through an encrypted overlay network rather than publicly exposed internet servers.
TON uses a 256-bit identifier instead of a common domain, which hides the IP address and communication port, thus making the actual server infrastructure more difficult to detect, block, or take down.
“Typical domain deprecation is ineffective because user endpoints do not rely on the public DNS system and instead exist as TON .adnl identities resolved within the overlay network itself,” ThreatFabric explains.
“Traffic pattern detection at the edge of the network sees only TON traffic, encrypted and invisible to any outgoing flows of TON-enabled applications.”
Source: ThreatFabric
TrickMo skills
TrickMo is a malware with a two-stage design: a host APK that acts as a loader and persistent layer, and a downloaded runtime APK module that implements the exploit.
The malware targets bank credentials with a phishing overlay, performs keystrokes, screen recording, and screen live streaming, SMS interception, OTP notification suppression, clipboard manipulation, notification filtering, and screenshot capture.
ThreatFabric reports that the new variant adds the following commands and abilities:
- curl
- dnsLookup
- ping
- telnet
- traceroute
- SSH tunnel
- remote port forwarding
- transfer through local port
- Certified proxy support for SOCKS5
The researchers also identified the Pine Runtime Hoking framework, which was previously used to block network performance and Firebase performance, but is currently inactive as no hooks are installed.
TrickMo also announces extensive NFC permissions and reports NFC capabilities in telemetry, but researchers have not found any effective NFC functionality.
Android users are advised to only download software from Google Play, limit the number of apps installed on their phones, use apps only from trusted publishers, and ensure that Play Protect is active at all times.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



