The official package of CheckMarx Jenkins is compromised with infostealer

Checkmarx warned over the weekend that its Jenkins Application Security Testing (AST) plugin has been published in the Jenkins Marketplace.
The compromise was claimed by the TeamPCP hacker group, which launched a supply chain attack that included Shai-Hulud campaigns via npm and a breach of the Trivy vulnerability scanner, which led to the delivery of stealth malware.
Jenkins is one of the most widely used Continuous Integration/Continuous Deployment (CI/CD) automation solutions for software development, testing, code scanning, application packaging, and deploying updates to servers.
The Checkmarx AST plugin in the Jenkins Marketplace integrates security scanning into automated pipelines.
“We are aware that a modified version of the Checkmarx Jenkins AST plugin was published on the Jenkins Marketplace. We are in the process of publishing a new version of this plug-in,” Checkmarx warned in an update.
This is the third incident in a series of attacks on the company’s supply chain security applications since late March.
According to offensive security engineer Adnand Khan, TeamPCP gained access to Checkmarx’s GitHub repositories and reverse-engineered the Jenkins AST plugin to deliver the data-stealing malware.
A company spokesperson confirmed to BleepingComputer that the threat actor obtained stored credentials from the Trivy supply-chain attack in March.
The message the hackers left in the about section: “Checkmarx fails to turn over secrets again. With love – TeamPCP.”
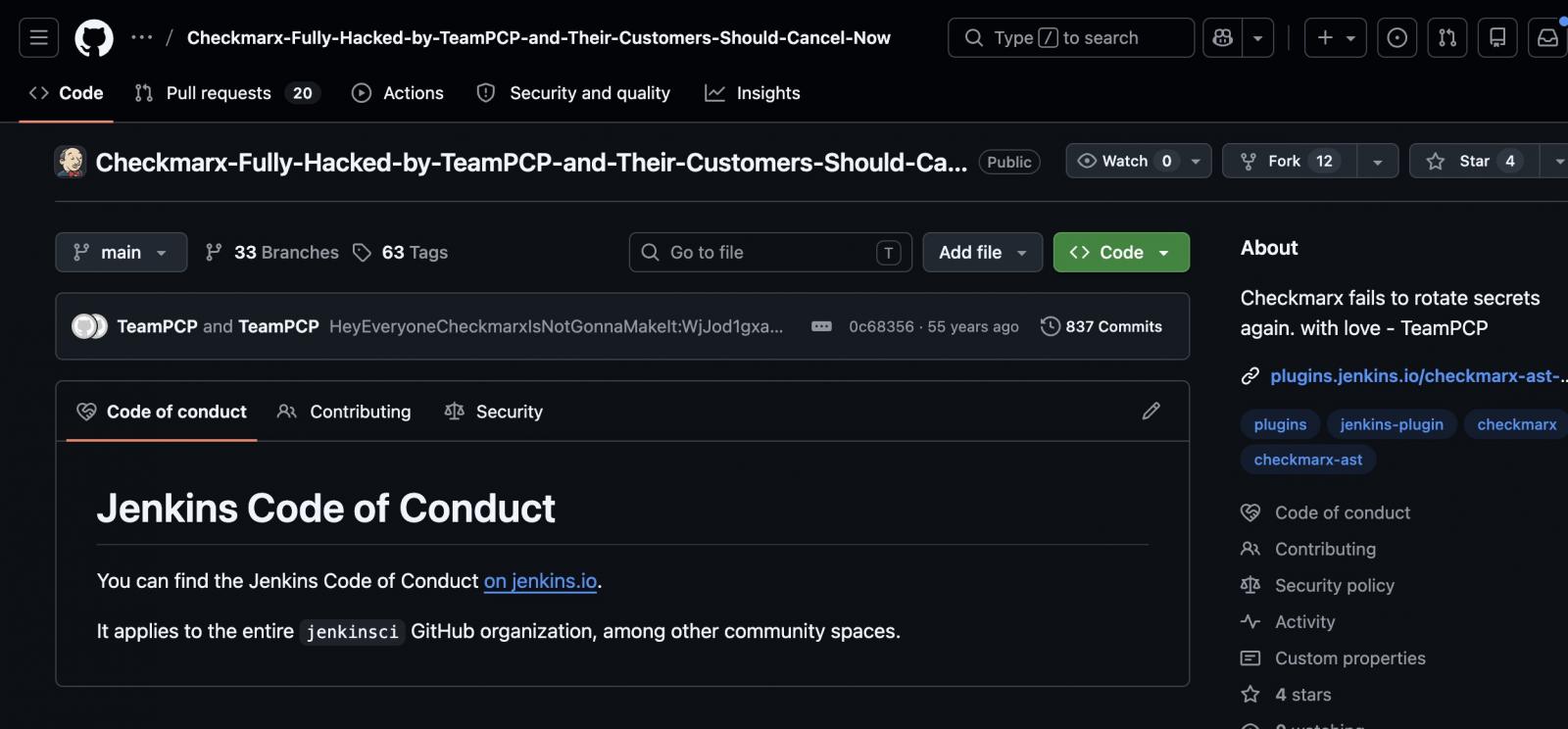
source: Adnan Khan
“As a result of that access, attackers were able to interact with Checkmarx’s GitHub environment and subsequently publish malicious code on certain objects,” a company spokesperson said.
Using the credentials stolen from the Trivy attack, the hackers published modified versions of several developer tools on GitHub, Docker, and VSCode that included information-stealing code.
The threat actor maintained access for at least a month and then published a malicious version of the company’s KICS analysis tool on Docker, Open VSX, and VSCode, which collected data from developer environments.
In late April, the company confirmed that the LAPSUS$ threat group leaked the stolen data from its private GitHub repository.
On Saturday, May 9, an incorrect version (2026.5.09) of the Checkmarx Jenkins AST plugin was uploaded to repo.jenkins-ci.org. The update was outside of the plugin release pipeline and included incorrect code.
In addition to not following the official date system, the malicious plugin lacked a git tag and GitHub release.
Checkmarx advised users to make sure they are using version 2.0.13-829.vc72453fa_1c16 of the plugin published on December 17, 2025, or older.
Although Checkmarx did not share any details about what the malicious Jenkins plugin does to the systems, those who downloaded the malicious version should consider their information at risk, rotate all secrets, and investigate any coordinated movements or persistence.
Checkmarx says its GitHub repositories are separate from its customer production environment, and no customer data is stored in the GitHub repository.
“We have been in contact with our customers throughout this process and will continue to provide relevant updates as more information becomes available,” the cybersecurity company said, adding that customers can find recommendations in the Support Portal or in the Security Updates section.
Checkmarx has published a set of malicious artifacts that defenders can use as indicators of compromise (IoCs) in environments.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



