Microsoft Exchange, Windows 11 hacked on day two of Pwn2Own
During the second day of Pwn2Own Berlin 2026, competitors collected $385,750 in prize money after running a unique 15-day giveaway on multiple products, including Windows 11, Microsoft Exchange, and Red Hat Enterprise Linux for Workstations.
The Pwn2Own Berlin 2026 hacking competition takes place at the OffensiveCon conference from May 14 to May 16 and focuses on business technology and artificial intelligence.
Security researchers can earn over $1,000,000 and rewards for hacking fully patched products in the web browser, enterprise applications, cloud/container, virtualization, virtualization, servers, local virtualization, and LLM categories.
According to Pwn2Own’s rules, all targeted devices are running the latest operating system versions, and all entries must compromise the target and show arbitrary code usage. Sellers have 90 days to patch their software and hardware after the zero-day disclosure at Pwn2Own.
The highlight of the second day was Cheng-Da Tsai (also known as Orange Tsai) of the DEVCORE Research Team who won $200,000 after fixing three bugs to get remote code execution with SYSTEM privileges on Microsoft Exchange.
Siyeon Wi also collected $7,500 after exploiting an integer bug to hack Windows 11, and Ben Koo of Team DDOS raised the rights to target Red Hat Enterprise Linux for Workstations for a cash prize of $10,000, while 0xDACA and Noam Trobishi used the NVIDIA-after-free bug to exploit the NVIDIA bug.
In the AI category, Le Duc Anh Vu of Viettel Cyber Security hacked Cursor AI coding agent for $30,000, Sina Kheirkhah of Summoning Team took down OpenAI Codex zero-day ($20,000), and Compass Security hacked Cursor ($15,000).
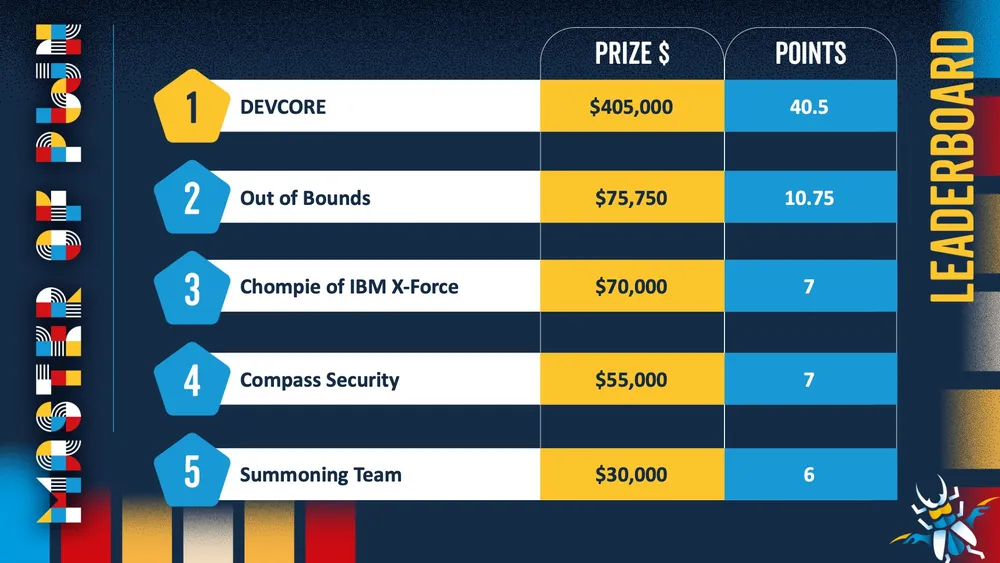
On the first day, Orange Tsai won another $175,000 after patching 4 Microsoft Edge sandbox escape bugs, while Valentina Palmiotti (chompie) of IBM X-Force Offensive Research collected $20,000 for cracking Red Hat Linux for Workstations and $50,000 for the NVIDIA Zero-dayki Toolkit.
Windows 11 was also hacked three times on the first day by Angelboy and TwinkleStar03 (working with the DEVCORE Internship Program), Kentaro Kawane of GMO Cybersecurity, and Marcin Wiązowski, each earning $30,000 in prize money for demonstrating zero-day exploit privileges.
On the third day of Pwn2Own, hackers will target Microsoft Windows 11, VMware ESXi, Red Hat Enterprise Linux, Microsoft SharePoint, and several coded AI agents.
The full schedule for day two and the results of each challenge is available here, while the full schedule for Pwn2Own Berlin 2026 is available here.
During last year’s Pwn2Own Berlin competition, TrendMicro’s Zero Day Initiative awarded 1,078,750 entries for 29 zero-day bugs and other bug fixes.

Automated testing tools deliver real value, but they’re designed to answer one question: can an attacker deploy on a network? They are not designed to check that your controls are blocking threats, your firewall detection, or your cloud configs.
This guide covers the 6 areas you really need to verify.
Download Now



