Bluekit’s new phishing service includes an AI assistant, 40 templates

A new phishing kit called Bluekit offers more than 40 templates targeting popular services and includes basic AI features for campaign draft generation.
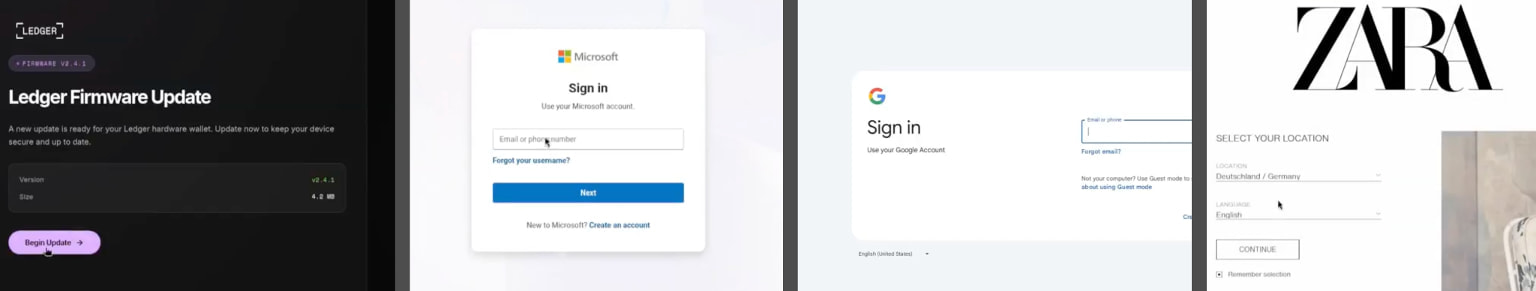
Available templates can be used to target email accounts (Outlook, Hotmail, Gmail, Yahoo, ProtonMail), cloud services (iCloud), developer forums (GitHub), and cryptocurrency services (Ledger).
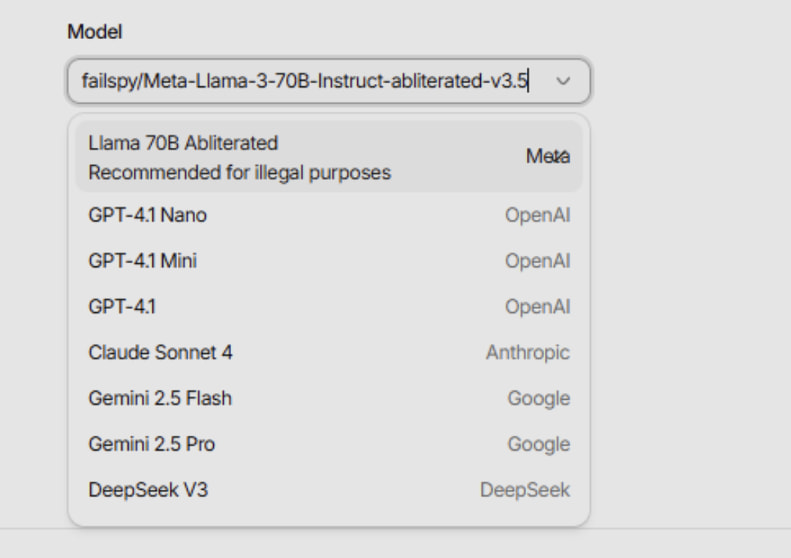
What makes the kit stand out is the presence of an AI Assistant panel that supports multiple models, including Llama, GPT-4.1, Claude, Gemini, and DeepSeek, which helps hackers write phishing emails.

This reinforces a broader trend of cybercrime platforms incorporating AI to target and augment their operations. Uncommon Security recently reported on ATHR, a phishing platform that uses AI agents to carry out social engineering attacks.
Cybersecurity company Varonis analyzed a limited version of Bluekit’s AI Assistant panel and notes that the results produced showed proxy content, suggesting the feature initially, in the testing phase.
“I [generated] the draft included a useful layout, but it still relied on standard link fields, QR blocks for the handler, and copy that would need to be cleaned up before use,” said Varonis.
“Bluekit’s AI assistant looked more like a way to frame a campaign than a finished phishing flow.”
Source: Varonis
Besides the AI feature, BlueKit integrates domain purchase/registration, phishing page setup, and campaign management into a single panel.
Varonis has reviewed templates for iCloud, Apple ID, Gmail, Outlook, Hotmail, Yahoo, ProtonMail, GitHub, Twitter, Zoho, Zara, and Ledger, featuring realistic designs and logos.
Source: Varonis
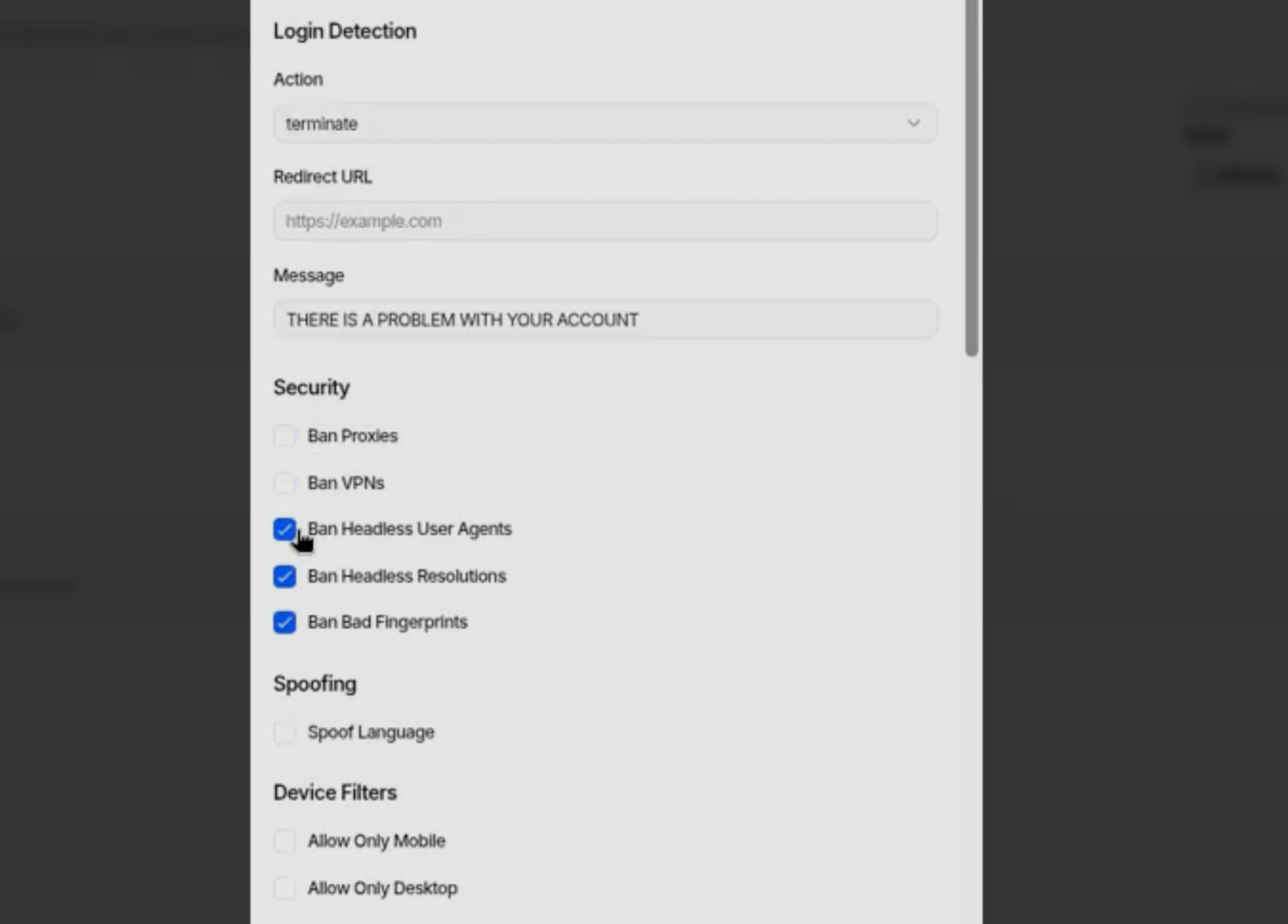
Operators can select domains, templates, and modes in a unified interface, configure phishing page behavior, such as redirects, anti-analysis methods, and login process management, and monitor victim sessions in real time.
Based on the options on the dashboard, users have granular control over the behavior of phishing pages and can block VPN or proxy traffic, headless user agents, or set up fingerprint-based filters.
Source: Varonis
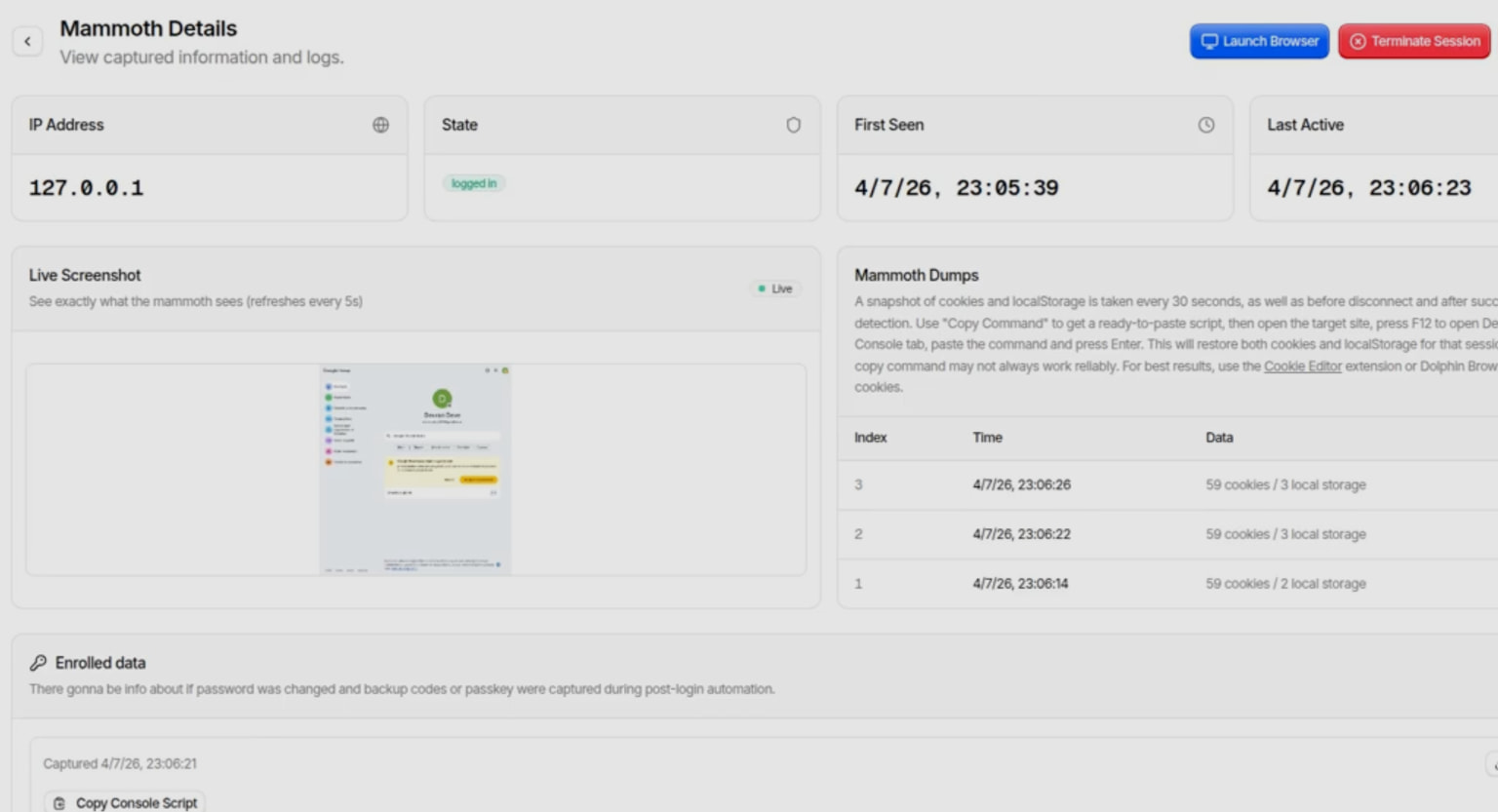
The stolen data is revealed through Telegram, on private channels accessible to operators.
Post-capture session monitoring includes cookies, local storage, and live session state, showing what the victim was served after logging in, helping operators fine-tune their attacks to be more effective.
Source: Varonis
Varonis notes that Bluekit is another example of an “all-in-one” phishing platform, giving low-level hackers complete tools to manage the entire lifecycle of a phishing attack.
.jpg)
Source: Varonis
However, the kit currently appears to be under active development, receiving frequent updates and evolving rapidly, making it a good candidate for increased adoption.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



