A critical Weaver E-cology bug has been used in attacks since March

Cybercriminals have been exploiting a critical vulnerability (CVE-2026-22679) in Weaver E-cology’s office automation since mid-March to execute discovery commands.
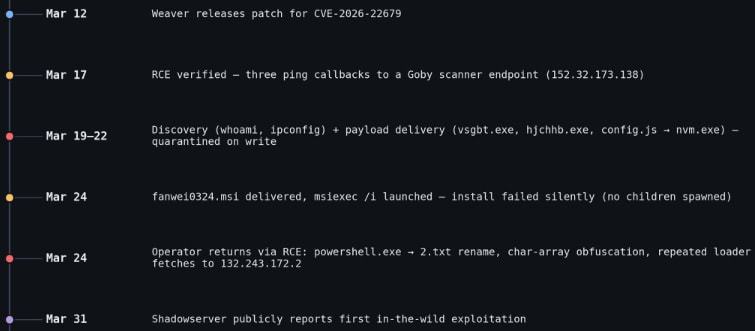
The attack began five days after the software vendor released a security update to address the problem, and two weeks before publicly disclosing it.
Researchers at the threat intelligence firm Vega documented the vicious cycle and reported that the attacks lasted about a week, each with several distinct phases.
Weaver E-cology is an enterprise office automation (OA) and collaboration platform used for workflow, document management, HR, and internal business processes. The product is mainly used by Chinese organizations.
CVE-2026-22679 is a critical remote code execution vulnerability affecting E-cology 10.0 builds before March 12.
The error is caused by a debug API endpoint that improperly allows user-supplied parameters to access a backend Remote Procedure Call (RPC) function without validation or input validation.
This allows attackers to pass crafted values that end up acting as system commands to the server, effectively turning the endpoint into a remote command execution interface.
According to Vega, the attackers first tested remote code execution (RCE) capabilities by executing ping commands from a Java process to a callback connected to Goby, then moved on to multiple PowerShell-based payloads. However, all this was blocked by endpoint protections.
Next, they tried to deploy the target MSI installer (fanwei0324.msi), but this failed to perform properly, and no trace activity was observed.
After those failed attempts, the attackers returned to the RCE repository, using an obfuscated and fileless PowerShell to redownload the remote scripts.
In all stages of the attack, the threat actors used inspection commands, such as whoami, ipconfig, and task list.
Source: Vega
Vega explains that while the attackers had an RCE opportunity through CVE-2026-22679, they never established a persistent session on the target host.
Users of Weaver E-cology 10.0 are recommended to apply security updates available from the vendor’s site as soon as possible.
“Every attacker process we’ve seen is parented by java.exe (Weaver’s Tomcat-bundled Java Engine), without prior authentication,” Vega explained, adding that “the vendor fix (build 20260312) removes the debugging endpoint entirely.”
There are no other mitigations or workarounds listed in the official bulletin, so the upgrade is the only recommendation.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



