The Palo Alto Networks zero-day firewall has been in use for about a month

Palo Alto Networks has warned customers that suspected government-sponsored hackers have been exploiting a critical PAN-OS firewall zero-day vulnerability for nearly a month.
Tracked as CVE-2026-0300, this remote code execution security flaw was discovered in the PAN-OS User ID Authentication Portal (also known as Hostage Portal) and stems from a buffer overflow vulnerability that allows unauthorized attackers to execute arbitrary code with root privileges PA-Series exposed on the Internet.
“We are aware of only a limited exploit of CVE-2026-0300 at this time. Unit 42 is tracking CL-STA-1132, a collection of potentially government-sponsored threat activities that exploit CVE-2026-0300. The attacker who created this activity exploited CVE-2026 to execute remote code (030eRC) on PAN-OS software,” the company said.
“Since April 9, 2026, there have been unsuccessful attempts to exploit the PAN-OS device. After a week, the attackers successfully found RCE against the device and installed shell code. Following the compromise, the attackers immediately cleaned the log to reduce detection by removing crash kernel messages, removing files of nginx core crashes and nginx crashes such as crash records and nginx crash.
After installing the victims’ firewalls, the attackers used the open source tunneling tools Earthworm and ReverseSocks5network, which can be used to create SOCKS v5 servers and proxy tubes on compromised devices, respectively.
The EarthWorm tool allows malicious actors to establish private communications across restricted networks, while ReverseSocks5 enables them to bypass NAT and firewalls by creating an outgoing connection from the target machine to the controller. EarthWorm has previously been used in attacks linked to CL-STA-0046, Volt Typhoon, UAT-8337, and Chinese-speaking threat groups APT41.
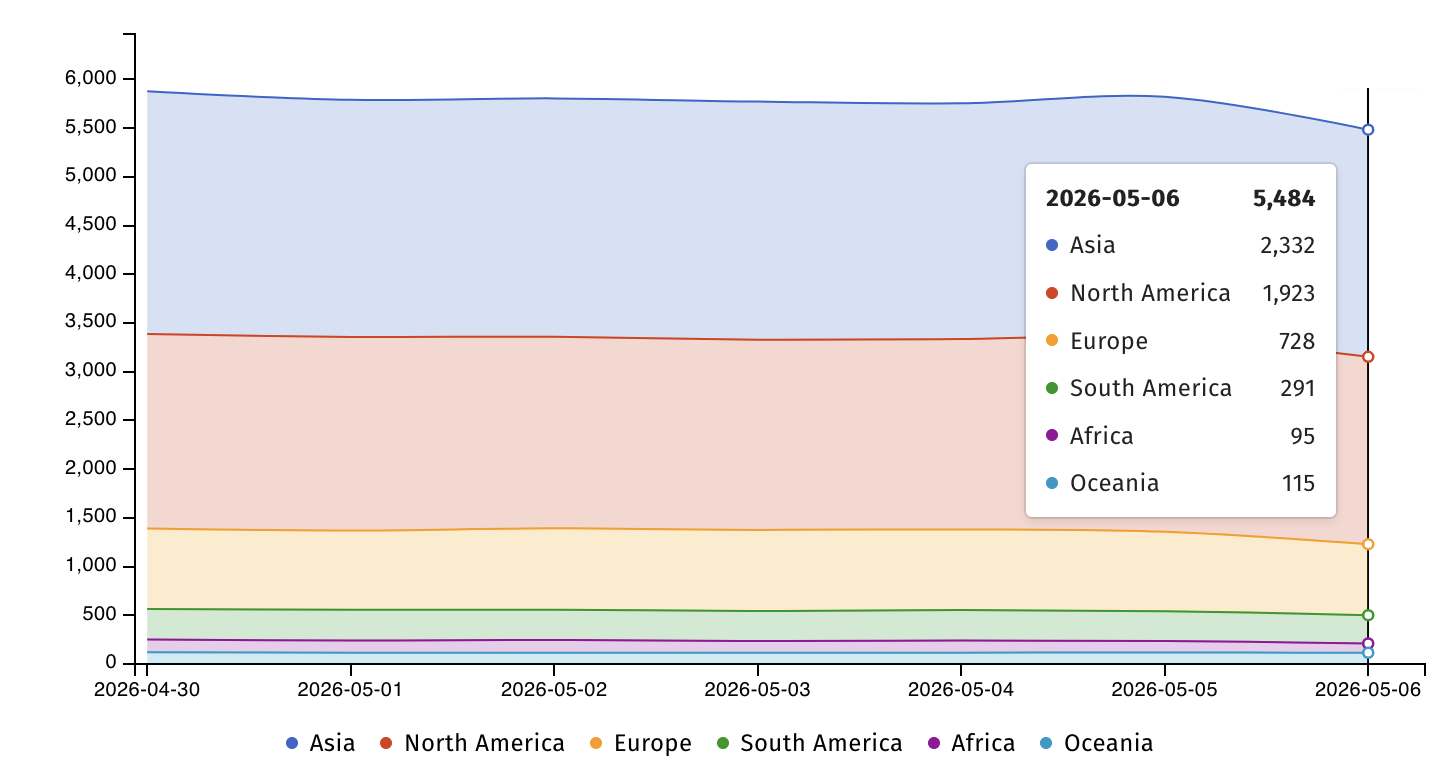
Internet threat monitoring Shadowserver now tracks more than 5,400 PAN-OS VM firewalls exposed on the Internet, most of them in Asia (2,466) and North America (1,998).
Palo Alto Networks told BleepingComputer yesterday that the bug does not affect Cloud NGFW or Panorama appliances and is still working on rolling out patches, with the first expected to be released next Wednesday, May 13.
Until security updates are available, the company “strongly” advises customers to secure access to the PAN-OS User-ID Authentication Portal by restricting access to trusted sites only, or by disabling the portal if that is not possible, which reduces the risk of this issue.
Administrators can quickly check that their firewalls are configured to run the vulnerable service on the User ID Authentication Portal Settings page, located under Device > User Identification > Authentication Portal Settings -> Enable Authentication Portal.
On Wednesday, the US Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2026-0300 zero-day to its catalog known as Known Exploited Vulnerabilities (KEV) and ordered the agencies of the Federal Civilian Executive Branch (FCEB) to protect vulnerable explosives on Saturday midnight, May 9.
This CVE-2026-0300 zero-day attack is part of a broader trend where threat groups are targeting edge network devices (e.g., firewalls, hypervisors, routers, and VPN software), which often lack logging and security software that protects endpoints.
In February, CISA also issued Binding Operational Directive 26-02, which requires US government agencies to remove network edge devices that no longer receive security updates from manufacturers.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



