Criminal IP and Securonix ThreatQ Collaborate to Improve Threat Intelligence Performance

Criminal IP partners with Securonix to integrate Criminal IP’s Threat Intelligence into ThreatQ, allowing organizations to integrate external IP intelligence into their existing operations, helping security teams accelerate analysis and respond in a more effective context.
Unlike traditional intelligence feeds, Criminal IP provides visibility into how assets and infrastructure are exposed across the Internet. By embedding this data into ThreatQ, organizations can add real-world context to investigations without disrupting existing processes.
ThreatQ centralizes and prioritizes threat data from multiple sources. With Criminal IP integration, organizations can enrich this data with proactive, exposure-based intelligence, strengthening investigation and response workflows without added complexity.
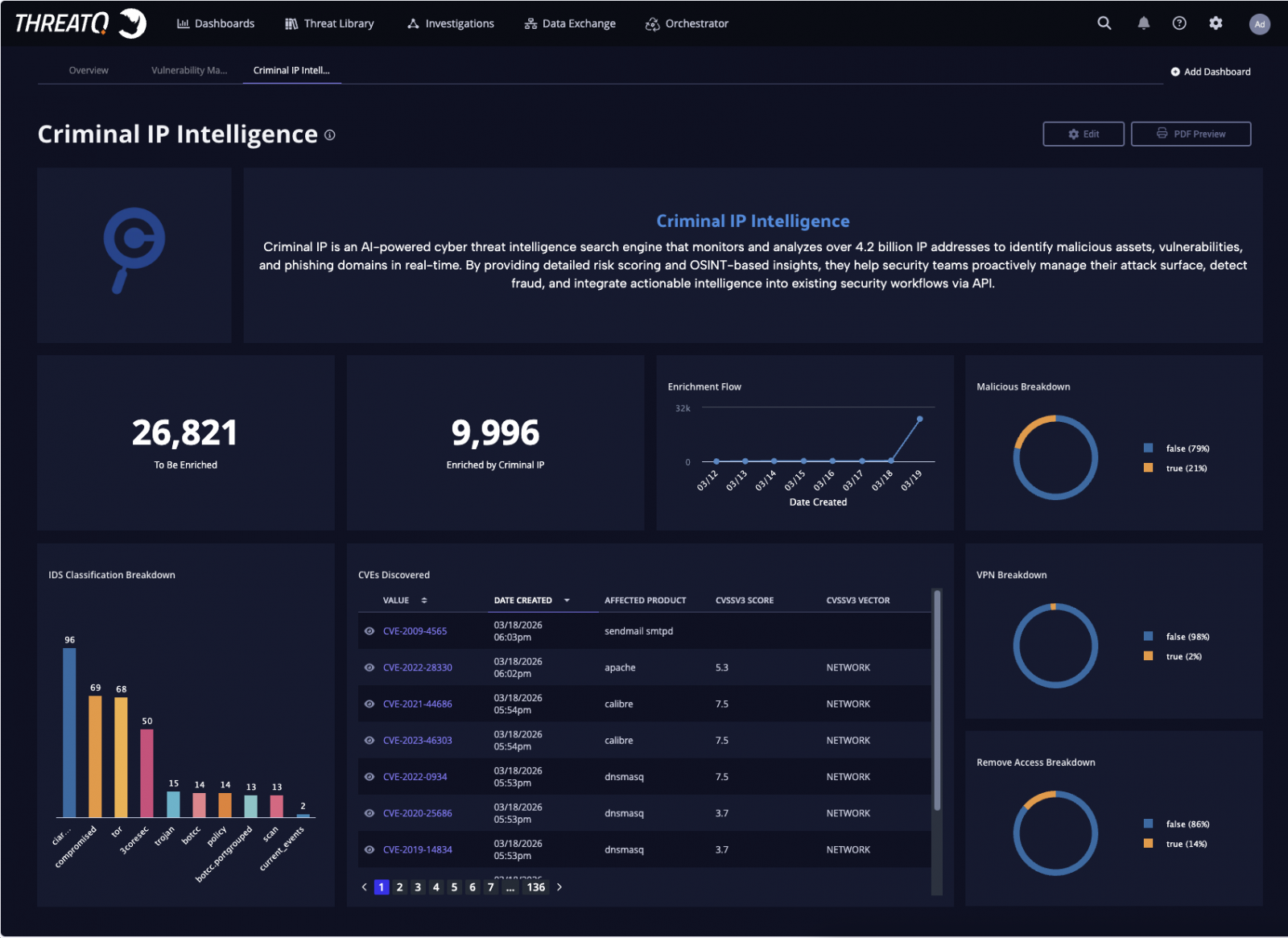
Automated Intelligence Enrichment at Scale
Within the integrated environment, Criminal IP’s intelligence APIs automatically enrich incoming IP addresses in ThreatQ with contextual data such as malicious scoring, VPN and proxy detection, remote access exposure, open ports, and known vulnerabilities.
Powered by ThreatQ’s data-driven orchestration engine, organizations can set up automated workflows that continuously check incoming leads against the Criminal IP threat database.
This ensures that the threat context remains current without requiring manual analysis effort, supporting rapid assessment and consistent prioritization.
Integrate Criminal IP exposure-based intelligence into ThreatQ to enrich IP indicators with real-time context.
Automated analysis of malicious targets, VPN/proxy detection, and infrastructure insights to accelerate investigation and response within unified workflows.
Check out Criminal IP Integration
Real-Time Investigations Within the Integrated Workplace
enabling unified visibility into improved indicators and risk context
The integration allows analysts to access Criminal IP intelligence directly within the ThreatQ interface, enabling real-time verification of suspicious IP activity without changing tools. By combining exposure data with infrastructure-level information, teams can effectively assess risk within existing workflows.
Analysts can also perform on-demand Criminal IP searches directly from the detailed view of directories or investigation boards, providing quick access to additional context during active investigations.
Criminal IP further enhances ThreatQ’s investigative graph by revealing relationships between IP addresses, associated infrastructure, and attack activity, helping analysts better understand connections and patterns across threats.
Intelligence-Driven Prioritization and Response
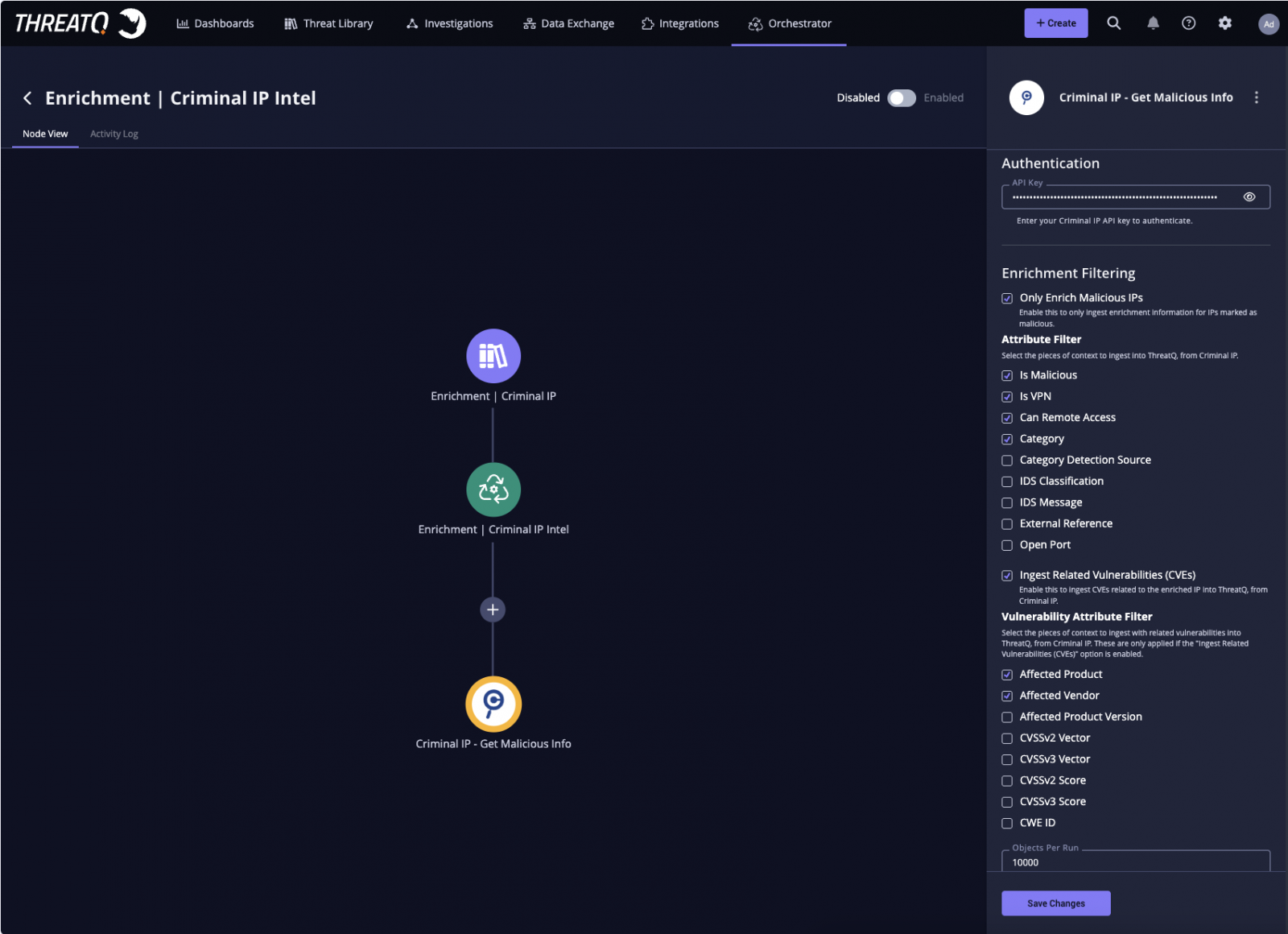
enabling automatic import and filtering of IP intelligence based on exposure directly to activity analysis
By integrating Criminal IP intelligence into the ThreatQ scoring framework, organizations can align risk assessment with their specific operating environment. This allows for more accurate prioritization and supports effective decision-making during investigations.
Advanced data can also be visualized through dashboards, providing clear visibility into malicious trends, VPN usage, and risk distribution in all directions.
Increasing Visibility Through Exposure Intelligence
The compilation highlights the growing importance of exposure-based intelligence in today’s threat analysis. By continuously monitoring and analyzing Internet-facing assets and IP infrastructure, Criminal IP provides differentiated visibility that goes beyond traditional index-based methods.
“This integration enables organizations to bring IP reputation and intelligence exposure directly to the ThreatQ platform, supporting rapid analysis and effective response throughout the investigation lifecycle,” said Byungtak Kang, CEO of Criminal IP. “By integrating our intelligence into existing workflows, security teams can improve visibility and make informed decisions without adding operational complexity.”
“This partnership strengthens the role of IP intelligence in critical areas of investigation and decision-making,” said Scott Sampson, Chief Revenue Officer, Securonix. “By combining ThreatQ’s orchestration and threat prioritization capabilities with Criminal IP real-time data, organizations can accelerate enrichment processes, reduce manual work, and focus on the most relevant threats in their environment.”
Through this partnership, Criminal IP and Securonix enable security teams to effectively deploy threat intelligence by integrating automated enrichment, workflow orchestration, and precision prioritization within the ThreatQ platform.
About Criminal IP
Criminal IP is a cyber threat intelligence solution powered by AI SPERA that provides decision-friendly IP address and domain reputation data to security teams worldwide.
By continuously scanning the global Internet, Criminal IP aggregates and transforms threat signals across IPs, domains, URLs, and attack infrastructure, covering malicious indicators, known vulnerabilities, exposed assets, and attacker behavior.
Criminal IP’s mission is to give organizations true visibility into their cyber environment and accelerate threat detection and response by delivering the intelligence needed to outsmart attackers. For more information, visit www.criminalip.io.
About Securonix
Securonix is transforming security operations with the industry’s first Integrated Security SIEM with Agentic AI, built to determine and act on the entire threat lifecycle with a human-inside-the-loop philosophy. Its cloud platform integrates discovery, investigation, and response, while enabling Sam, the AI SOC Analyst, and a production-based AI operating model for the SOC, so organizations can scale and manage AI through the analyst work it delivers. To help businesses become Breach Ready and Board Ready, Securonix delivers managed, results-driven security operations at scale. Recognized as a Leader in the Gartner® Magic Quadrant™ for SIEM and Customer Choice by Gartner Peer Insights™, Securonix delivers trusted security services to businesses worldwide. Learn more at www.securonix.com.
Sponsored and written by Criminal IP.