VECT 2.0 cracked ransomware works as a data feature for large files

Researchers warn that the VECT 2.0 ransomware has a problem with the way it handles encryption nonces which results in permanently destroying large files rather than encrypting them.
VECT has been advertised in some of the latest BreachForums iterations, inviting registered users to become their contacts, and distributing access keys via private messages to those who have expressed interest.
At one point, VECT operators announced a partnership with TeamPCP, a threat group responsible for the latest supply-chain attacks affecting Trivy, LiteLLM, and Telnyx, as well as the European Commission attack.

In the announcement, the VECT operators stated that their goal was to exploit the victims of those supply-chain compromises, send ransomware payloads to their sites, and carry out massive supply chain attacks against other organizations.
.jpg)
Source: Check Point
Flawed ransomware
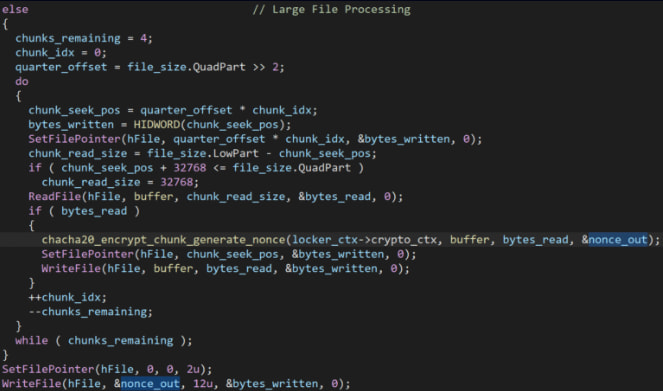
Although this is intended to increase the speed of encryption for large files, because all chunk encryptions use the same memory buffer for random output, each new nonce overwrites the previous one.
Once all bits have been processed, only the last nonce generated remains in memory, and only that one is written to disk.
As a result, the only part of the file that can be recovered is the last 25%, the first three parts cannot be reversed, as the nonces are lost.
Those lost nonces are not transmitted to the attacker either, so even if the VECT operators wanted to decrypt the files of the ransom paying victims, they wouldn’t be able to.
Source: Check Point
Although this is intended to increase the speed of encryption for large files, because all chunk encryptions use the same memory buffer for random output, each new nonce overwrites the previous one.
Once all bits have been processed, only the last nonce generated remains in memory, and only that one is written to disk.
As a result, the only part of the file that can be recovered is the last 25%, the first three parts cannot be reversed, as the nonces are lost.
Those lost nonces are not transmitted to the attacker either, so even if the VECT operators wanted to decrypt the files of the ransom paying victims, they wouldn’t be able to.
.jpg)
Source: Check Point
Checkpoint notes that, since most business-critical files, including VM disks, database files, and backups, are larger than 128kb, the impact of VECT as a data eraser can be catastrophic in many areas.
“At a threshold of only 128 KB, smaller than a typical email attachment or office document, what the code classifies as a large file includes not only VM disks, databases, and backups, but regular documents, spreadsheets, and mailboxes. In fact, almost nothing the victim would care to recover falls under this threshold,” Check Point said.
The researchers found that the same misbehavior is present in all variants of VECT 2.0 ransomware, including Windows, Linux, and ESXi, so the same behavior of data deletion applies in all cases.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



