Social engineering in information and cybersecurity
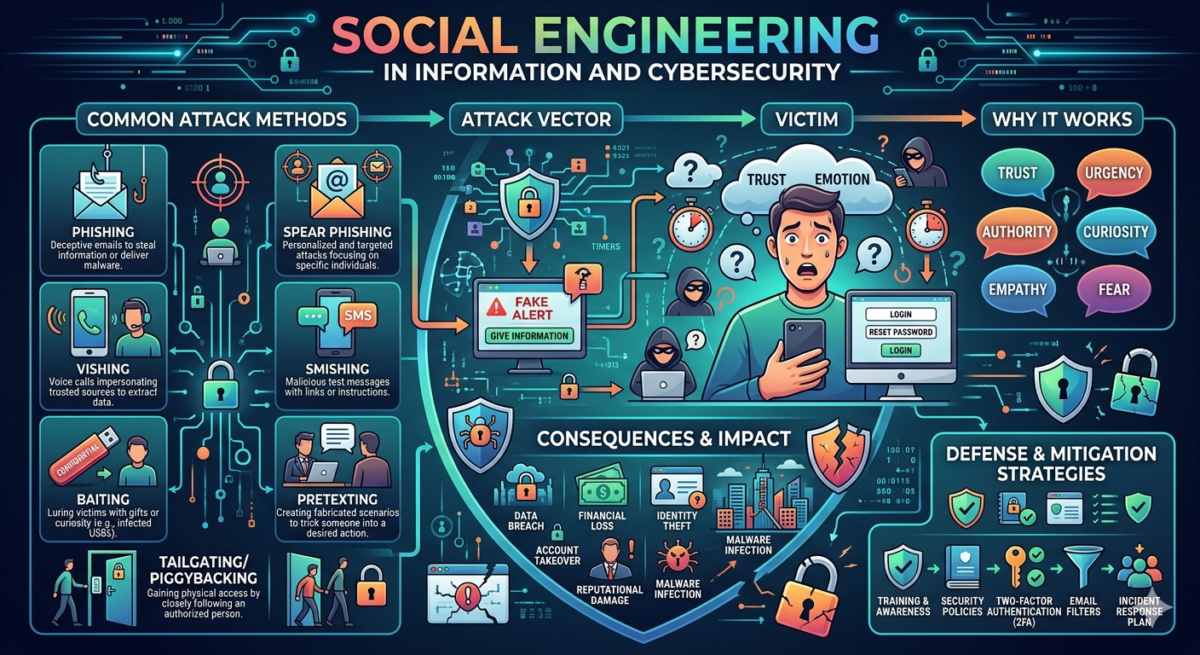
Human-based attacks (social engineering) remain the most popular method of cyberattacks against both organizations (50%) and individuals (91%, according to penetration testing data for Q1 2023). Phishing emails and web pages that are exact copies of real ones are most often used for this purpose. In this article, we will explain what social engineering is in the context of information security, what typical attacks using it look like, and how to protect against them.
Table of Contents
What is social engineering in simple terms?
Social engineering in the context of cybersecurity is a category of crimes that relies on psychological insight and subtle manipulation of people to achieve a goal. For more information on other types of threats and protective measures, see “ Types of Information Security .”
An example of such manipulation: an attacker wants to penetrate a company’s infrastructure but lacks the hacking expertise to gain access using malicious code. Instead, they send a convincing-looking email to an employee, posing as a manager or colleague, asking for the necessary login credentials.
This type of crime requires only the ability to gain someone’s trust, even though the negative consequences can be comparable in damage to “real” hacking. A security audit can help reduce the likelihood of a classic hacker attack. However, only knowledge of all the specifics of this threat can protect against social engineering.
It’s worth noting that, broadly speaking, social engineering and manipulation can also be used for positive purposes—for example, this is how any motivational coach operates. In this article, we will focus only on the negative practical applications of these techniques.
How does social engineering work?
All social engineering works according to the same simple pattern: gathering information, finding the best method of influence, making contact, achieving the goal, breaking contact.
What does a social engineer do?
The main goal is to understand what motivates the user, what frightens them, or what triggers other emotions that drive them to do what the manipulator wants. As a rule, criminals who professionally engage in social engineering are skilled psychologists and know how to skillfully adapt their actions to the information context and the specifics of a particular target.
For example, knowing the communication styles in a particular organization, it is much easier to achieve a goal by imitating the manager’s communication style than by trying to extract information using an average template of a “motivational” text.
Once a social engineer has figured out what motivates his target, the job is half done—all he has to do now is rely on the target’s gullibility and suggestibility.
Social engineering attack cycle
Most forms of social engineering can be described within a four-step cycle.
1. Preparation
During the preliminary stage, the attacker collects as much data as possible about the victim or organization, learns the specifics of its operations and processes, and notes all details that could be useful for infiltration. The collected data is used to establish contact in the next step.
2. Penetration
The fraudster establishes contact with the chosen person, uses social engineering techniques, and gains their trust by posing as someone they are not.
3. Operation
The entire scheme is designed to lead the victim to perform a “target action.” For example, this could be clicking on a malicious link in an email, entering confidential data in an email or form on an external website, or opening an attached archive containing malware.
4. Exit
Once the victim has performed the desired action, the scammer stops communicating (in the case of phishing emails, communication is not expected from the start). The social engineer has obtained what they wanted, and now they will exploit the acquired data for their own gain.
If a scammer doesn’t get what they want on the first try, that doesn’t mean they’ll give up. A social engineer will likely try new ways to “get the key” to their intended victim.
Who might be a target of social engineering?
These practices are most likely to target ordinary office workers, management, and accounting staff, while IT specialists and security personnel are less likely to be targeted. Attackers often impersonate the latter, exploiting their authority and demanding that their “colleagues” provide certain information, for example, to verify their accounts or perform maintenance.
A social engineer’s primary weapon is emotional appeal. Social engineering, especially phishing, is never emotionally neutral—it always exploits vulnerabilities in the human psyche, those associated with strong emotions that cause the victim to behave irrationally.
The main emotions exploited.
Fear – the social engineer insists that if the victim fails to perform the target action, there will be serious consequences. Variations are numerous, ranging from the threat of losing access to their email to a fake notice of a court fine, which, if not paid, will allegedly lead to seizure of property.
Curiosity – this type is often mixed with fear and is also based on current news events. For example, a data breach becomes publicly known, and the victim receives a phishing email asking them to check themselves and their contacts against a published database. If the victim clicks the link and enters their personal information or passwords, they will end up in the hands of the attackers, making the breach real for the individual user.
Greed – Phishing messages in email, social media, and instant messaging exploit the theme of lottery winnings, product discounts, the opportunity to earn cryptocurrency, tax deductions, and similar monetary incentives. They emphasize that the prize, discount, or winnings will disappear if you don’t act quickly (the phishing site typically uses a fake timer for this purpose). In this case, the scammers rely on the fact that most people are interested in the opportunity to make easy money—and judging by the popularity of such scams, they will always be relevant.
Urgency is an additional factor that influences the victim. Attackers cite loss of access to a service, problems at work, or legal issues as reasons for taking action immediately—the latter is especially true when the social engineer impersonates letters from the police, the tax office, or other similar authorities.
What are examples of social engineering?
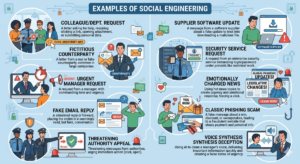
- A letter from a colleague, security officer, accounting department, or new employee asking for help, which requires clicking a link, opening an attached file, or submitting personal information.
- A letter from a counterparty, real or fictitious (the latter is more appropriate for large companies).
A request from a manager, addressed in a commanding tone, with an urgent request. - A message simulating a reply to a previously sent email or forwarded to the victim by another employee of the organization. In this case, the victim finds themselves in the middle of someone else’s conversation, which can happen frequently in large organizations, and is unable to discern that the message is fake, after which they perform the intended action.
- An appeal from the police, tax authorities, the prosecutor’s office, or other authorities that is threatening in nature and urges you to immediately click on a link or open an attached file.
- A message from a supplier of some specialized software used at an enterprise, usually related to the need to supposedly update it by following a link or downloading a file.
- A message from a security service or service used at the enterprise, demanding a current login and password under the pretext of technical work on the system.
- Using a current, emotionally charged news story (COVID, mobilization, legislative changes) to force the victim to click on a link and view a document that allegedly could determine their future life.
- A classic phishing scam involves a message about a win, discount, or sweepstakes, followed by a redirect to a fake website that mimics the real thing. In this case, both personal and payment information entered by the user is stolen.
- Using new technologies, such as voice synthesis, to tell a manager that he needs to know some important information as quickly as possible.
The dangers of social engineering
- Loss of personal data.
- Loss of payment information or funds.
- Loss of an organization’s confidential data or violation of its commercial secrets.
- Leak of employee passwords.
- Leak of company user/client databases.
- Infection of computers and gadgets with malware has an unpredictable range of consequences, from data encryption to theft or destruction, to the shutdown of an organization or production facility.
- Industrial espionage.
- Using hacked accounts for further social engineering on behalf of a compromised company or individual.
Types of social engineering attacks
The most popular types of social engineering:
Phishing is the undisputed champion of all social engineering attacks. A distinction is made between spam phishing, which targets a broad audience; spear phishing, which targets a specific individual or organization; and personal phishing, the most expensive and complex to execute, which targets a single individual based on their specific characteristics. The most popular channels are email, social media, SMS, instant messaging, and voice messages. Phishing can also be used in search engines, where ads are purchased in search results to insert malicious links. Such phishing links can often remain up for quite a while before being detected and removed by security services.
Baiting is a luring attack that exploits greed and entices you to enter your payment or personal information or download a file on an external website. Typically, you either lose data or your device becomes infected with malware—or sometimes both.
Pretexting is a type of phishing whereby contact is established with the victim, and their trust is gained. It is often used on the external internet, for example, on dating sites, but can also be used for specific purposes via instant messaging apps.
“Quid pro quo” is a type of baiting where you’re promised a gift or reward for participating, for example, in a survey or providing your personal information under some other pretext. The problem with this method is that it’s often used quite legally for marketing purposes.
Scareware is a very old attack method in which the victim is convinced that their computer or device has been infected with malware, or that their account has been hacked and therefore needs to take immediate action. Scareware exists, among other forms, in the form of online banner ads or as a sideload from downloaded pirated software. Often, the victim is convinced to download a fake anti-threat app, which turns out to be fully functional malware.
Watering hole attacks are called “watering holes” because they simultaneously affect multiple users accessing a previously secure website. A typical example: an organization’s website, built on a popular platform like WordPress and not updated in a while, is injected with a malicious script through a zero-day vulnerability, which begins downloading malware to the computer of every user who accesses it. If the site is relatively popular, this can cause significant damage before the vulnerability is patched.
5 Signs of Social Engineering. How to Recognize an Attack
Signs of social engineering include:
- Emotional pressure. The sender or caller appeals to emotions, particularly fear, and insists on the urgency of completing the target action.
- Suspicious emails. In the case of email, the email appears suspicious: it has an unusual signature, the text contains errors or character substitutions, the style is inconsistent with the sender’s usual tone, and the sender’s address appears suspicious.
- Messages on social media from people you haven’t contacted in a while. This person is writing to you and wants something from you (for example, help). An unusual tone and an emphasis on urgency also indicate fraud.
- Phishing sites. If you’ve landed on a site from messages from unknown recipients, pay attention to its design, registration date, and whether most of it is a stub or copied material.
- Suspicious attachments in the email. For example, an archive or executable file (.exe, .bat, etc.). The file name may be misspelled, contain foreign characters, or simply not match the accompanying text.
Methods of protection against social engineering
Key defenses against social engineering include various approaches and measures aimed at preventing such attacks.
- Never share your account logins and passwords with anyone.
- Do not open emails or attachments from suspicious sources.
- Don’t rush to click on links to suspiciously profitable offers with time limits.
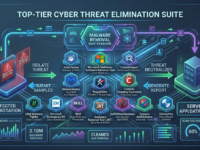
- Use antivirus software on all devices and update it regularly.
- Implement dedicated anti-phishing technical solutions that will block most of these messages.
- Check your devices for viruses regularly.
- Use complex passwords, or better yet, password managers.
- Conduct anti-phishing training and testing of employees to ensure they have mastered the information.
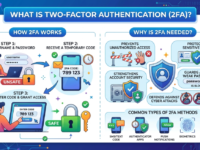
- Set up two-factor authentication.
- Separate access levels within the organization and ensure database security.
- Avoid using personal technology for work purposes if you work remotely, practice digital hygiene, and regularly check your devices for compromise.
What to do if you’ve become a victim of social engineering
Payment data theft: Contact your financial service provider and report the fraud so they can protect your funds. You will likely need to reissue your card.
Malware infection: Report it to your security team so they can take corrective action. If your company doesn’t have an in-house security team, you should contact a cyberattack mitigation professional.