The Importance of Cybersecurity

Just as you protect your home by locking the door when you leave, you should protect your network and computer with cybersecurity.
What is cybersecurity?
Cybersecurity refers to internet-connected defense systems that protect against cyber threats. It protects software, data, and hardware and helps prevent cybercriminals from gaining access to devices or networks.
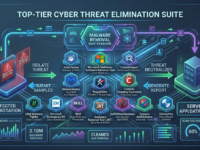
Various components of cybersecurity
The best cybersecurity solutions are comprehensive and cover all aspects:
- Application security
- Cloud security
- Data security
- Endpoint security
- Identity management
- Infrastructure and database security
- Mobile security
- Network security
- Business security
It should also include disaster recovery planning or business continuity planning, which outlines recommendations for business recovery from future cyberattacks, as well as preventative methods such as employee training.
Cybersecurity: Why it matters
The importance of cybersecurity stems from the desire to ensure the privacy and security of information, data, and devices. In modern society, people store large amounts of data on computers and other internet-connected devices. Much of this data is sensitive, such as passwords and financial information.
If cybercriminals gain access to this information, they can create several problems: sharing sensitive information, using passwords to steal funds, or even modifying the data to gain some kind of profit.
Businesses need cybersecurity to protect their data, finances, and intellectual property. Individuals need it for similar reasons, although intellectual property is less of a concern, and there’s a greater risk of losing important files, such as family photos. For public or government organizations, cybersecurity can help ensure the continued existence of society. For example, if a cyberattack targets a power plant, it could cause a citywide blackout. If an attack targets a bank, criminals could steal from hundreds of thousands of people.
Benefits of Cybersecurity
By implementing cybersecurity, your business can protect itself from a number of cybersecurity threats described below, as well as countless other existing threats.
With cybersecurity, your business won’t have to worry about unauthorized users gaining access to networks or data. This will help your business protect both end users and employees.
Even in the rare cases where cybersecurity fails to prevent an attack or breach, it improves recovery times. Furthermore, many companies notice that customers and developers trust their products more if they include a robust cybersecurity solution.
Types of cybersecurity threats
There are dozens of cybersecurity threats, but the most common ones are listed below.
DDoS attacks
A distributed denial-of-service attack occurs when cybercriminals take over a network or its servers by sending too much traffic. This prevents the network from processing valid requests and renders the entire system inoperable. It can completely disrupt the operations of organizations.
Malicious programs
This malware can include computer viruses, spyware, Trojan horses, worms, and other programs or files that can harm a computer. Malware is often distributed through downloads that appear legitimate or through email attachments.
Within the malware category, there are different types of cybersecurity threats:
Adware is advertising software that distributes malware.
Botnets are networks of multiple computers infected with malware. Cybercriminals use them to perform online tasks without the user’s permission.
Ransomware – locks data and files and threatens to leave the files locked or delete them unless the victim sends payment.
Spyware records user behavior, such as collecting credit card information.
Trojans are malicious programs disguised as legitimate software. Once downloaded, they collect data or cause damage.
Viruses self-replicate and attach themselves to files, which then spread throughout the computer system.
Man-in-the-middle attacks
This type of attack involves a cybercriminal intercepting conversations or data transfers between people. An example would be a cyberattack using an unsecured Wi-Fi network to intercept data sent from a victim’s computer to the network.
Phishing
This type of cybersecurity threat sends fake emails from seemingly legitimate sources to obtain credit card information or passwords.
Social engineering
This type of attack tricks users into violating security procedures through human interaction. Cybercriminals often combine social engineering attacks with other attacks, such as phishing, to increase the likelihood that victims will click a link or download a file.
SQL injection
SQL stands for Structured Query Language. SQL injection is a technique used to manipulate and potentially steal data in databases. It involves inserting malicious code into SQL queries that exploits weaknesses in data-driven applications.
Cybersecurity problem
It’s constantly evolving. Perhaps the biggest challenge in cybersecurity is the constant advancement of technology, which gives cybercriminals a constant opportunity to test new potential vulnerabilities. To make matters even more challenging, cybercriminals are constantly developing new methods of conducting cyberattacks.
As a result, software and cybersecurity experts are constantly developing new solutions to patch potential vulnerabilities, while cybercriminals continue to find new attack methods. Thus, cybersecurity is constantly evolving.
Organizations typically find it incredibly challenging to stay current with the ever-evolving cybersecurity landscape—it can be costly. This requires constant security awareness and regular updates.
Data volume
Another serious cybersecurity concern is the volume of data held by most businesses. The more data, the more attractive a company becomes, especially if that data contains sensitive information. This not only exposes the people whose data the company stores to the risk of data theft but also exposes the company to legal action if the data is stolen due to negligence.
The need for education and training
Another challenge is that relying solely on cybersecurity software and other solutions is impossible: user training is also crucial. Employees must understand that their actions carry risks, such as opening links from unknown emails or accidentally infecting a smartphone with malware. This requires time taken away from their regular duties for training, and companies must allocate a budget for this training.
Insufficient number of cybersecurity experts
Among other problems, there is currently a shortage of cybersecurity specialists. By some estimates, up to two million cybersecurity jobs remain unfilled worldwide. This problem is being addressed to some extent by machine learning and other technological advances, but it remains a significant obstacle.