The US government is looking for evidence of a plan for the massive Canvas cyberattack

The U.S. House Committee on Homeland Security is asking Department officials to testify about two cyberattacks by the ShinyHunters hacker group that targeted the Canvas company platform, allowing threat actors to steal student information and disrupt schools during final exams.
In a letter sent Monday afternoon to Instructure CEO Steve Daly, Homeland Security Committee Chairman Andrew R. Garbarino said the committee is investigating the Instructure breach affecting millions of students.
“The Homeland Security Committee (Committee) is investigating reports regarding recent cybersecurity incidents affecting Instructure Holdings, Inc. and the tens of millions of students, teachers, and administrators who rely on the Canvas learning management platform,” the letter read.
“Within one week, a group of cybercriminals known as ShinyHunters breached Instructure twice.”
As first reported by BleepingComputer, Instructure disclosed on May 3 that it had breached the law. The company later confirmed that it had caught the hacker on April 29 after malicious actors disrupted its systems and stole the information of students and school staff using Canvas.
The company said the disclosed information included names, email addresses, student ID numbers, and messages sent between students and teachers on the platform. However, the data did not include passwords, financial information, or government identifiers.
On May 3, the ShinyHunters gang claimed responsibility for the attack, telling BleepingComputer that it stole 280 million data records from 8,809 colleges, school districts, and online education sites.
The threat actor shared a list of affected educational institutions, with stolen records ranging from tens of thousands to several million at each institution.
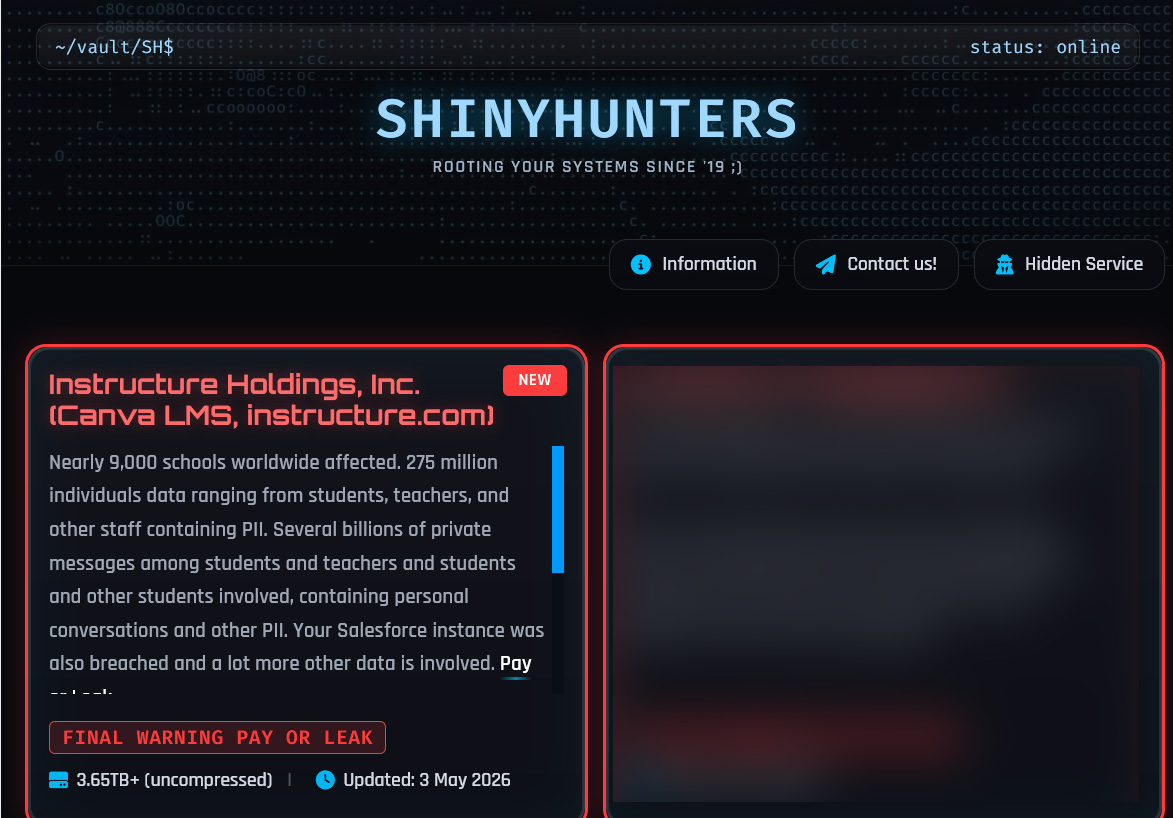
Source: BleepingComputer
The ShinyHunters group carried out a second attack that destroyed Canvas login sites at schools and universities across the United States, displaying phishing messages demanding that Instructure negotiate with the group. The disruption affected institutions in many states during final exams and end-of-semester activities, forcing some colleges to cancel exams.
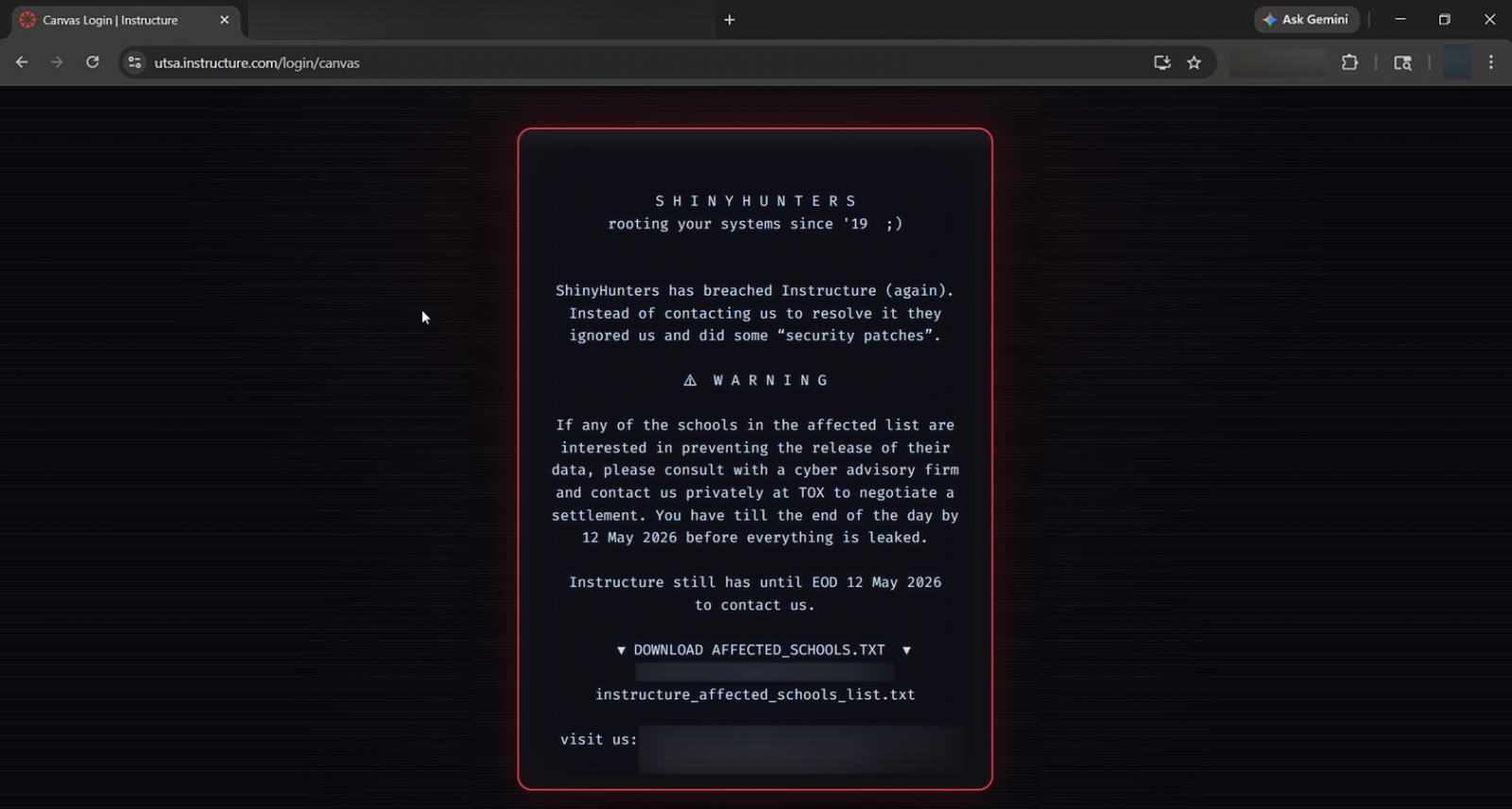
Source: BleepingComputer
BleepingComputer later discovered that malicious actors were exploiting a cross-site scripting (XSS) vulnerability to gain authenticated administration sessions and modify login portal pages.
According to a letter from the Homeland Security Committee, schools in California, Florida, Georgia, Oklahoma, Oregon, Nevada, North Carolina, Tennessee, Utah, Virginia, and Wisconsin have reported disruptions related to the incident.
The committee also talked about the messages posted by the attackers saying that they also targeted Instructure because the company refused to negotiate with the group.
Last night, shortly after ShinyHunters inexplicably removed Instructure from its data leak site, the company revealed that it has reached an agreement with ShinyHunters to stop the public leak and ensure that the stolen data is removed.
While the company did not specifically say it paid the ransom or directly confirm BleepingComputer’s questions about the matter via email, hacking groups rarely agree to remove stolen data or stop leaks unless some form of payment or agreement is reached.
The gang also updated its database of data leaks today, with a new statement saying the information has been declassified and there is no need for schools to contact them privately to discuss it.
“We have nothing to add or comment on the latest situation at the LMS company. If you are the affected institution, we do not want your money. Please stop all attempts to contact us, the matter has been resolved,” read the ShinyHunters update.
“The company and its customers will not be further directed or contacted for payment. Details are not available.”
The Homeland Security Committee said the repeated compromises raise “difficult questions” about the company’s ability to respond to incidents and its obligations to properly protect the data it stores.
The committee requests that Instructure or a senior company representative participate in a forum before May 21 to discuss both the intrusion, the stolen data, its storage and notification efforts, and communication with government agencies.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



