A new BlackFile scam group linked to the rise of vishing attacks

A new financially motivated hacking group known as BlackFile has been linked to a wave of data theft and targeted attacks against retail and hospitality organizations since February 2026.
The group, identified as CL-CRI-1116, UNC6671, and Cordial Spider, poses as IT company help desk workers to steal employee information and demand seven-figure ransoms, according to information shared by cybersecurity firm Palo Alto Networks’ Unit 42 and Retail & Hospitality Information Sharing Center (ISAC) ShaRing Center Information Sharing.
Unit 42 security researchers have also linked BlackFile with moderate confidence to “The Com,” a network of English-speaking cybercriminals known for targeting and recruiting young people for extortion, violence, and the production of child sexual exploitation material (CSAM).

In a report on Thursday, RH-ISAC said that the group’s attacks begin with calls to employees from fraudulent numbers, where threatening actors pose as IT support to lure employees to enter the login pages of fraudulent companies asking them to enter their credentials and one-time codes.
“Attackers behind CL-CRI-1116 use phishing (vishing) from rogue Voice over Internet Protocol (VoIP) numbers or fake Caller ID Names (CNAM) as a form of social engineering, often impersonating IT support staff,” RH-ISAC said.
“We can confirm that we are seeing a significant increase in Blackfile issues and that TTPs appear to be very similar to groups like ShinyHunters and SLSH and similar copycats that use social engineering data tactics,” CyberSteward founder and CEO Jason ST Kotler also told BleepingComputer.
Using stolen credentials, BlackFile attackers registered their own tools to bypass multi-factor authentication, then increased access to high-level accounts by deleting internal employee directories.
BlackFile steals data from victims’ Salesforce and SharePoint servers using standard API functions, specifically searching for files containing words like “secret” and “SSN.”
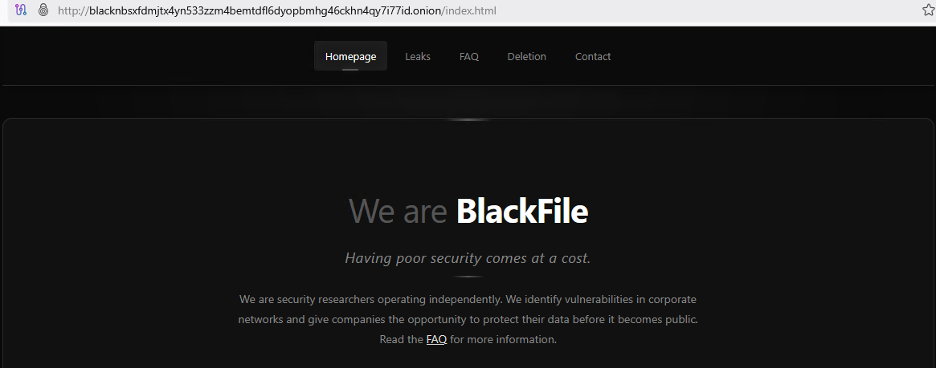
The classified documents are downloaded from servers controlled by the attackers and published on the dark web of the gang’s data leakage before victims receive ransom demands through the email accounts of vulnerable employees or randomly generated Gmail addresses.
“Using Salesforce API access and standard SharePoint download functions, attackers delivered large volumes of data – including CSV data sets of employee phone numbers and confidential business reports – to attacker-controlled infrastructure,” RH-ISAC said.
“This is often done under the guise of legitimate SSO-authorized sessions to avoid triggering simple user agent notifications.”
Employees of vulnerable companies (including senior executives) have also been victims of phishing attempts, which include making fake emergency calls to responders. Attackers often use this tactic to pressure their victims.
Mandiant also told BleepingComputer that they are actively responding to several fraud incidents that led to data theft and fraud, including one involving the now-offline victim-shaming site BlackFile.
To reduce the success rate of BlackFile attacks, RH-ISAC recommends that organizations strengthen their call-holding policies, enforce multi-factor authentication for callers, and conduct simulation-based social engineering training for front-line staff.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



