ConsentFix v3 attacks Azure with an automated OAuth exploit

A new type of attack, called ConsentFix v3, has been making the rounds in hacker forums as an advanced form of attack on Microsoft Azure.
The first version of ConsentFix was launched by Push Security last December as a ClickFix variant of the OAuth phishing attack, which tricks victims into completing a legitimate Microsoft login flow through the Azure CLI.
Using social engineering, the attacker tricked victims into pasting a host URL containing an OAuth authorization code that can be used to obtain tokens and steal an account without passwords, without multi-factor authentication (MFA).
ConsentFix v2 was developed by researcher John Hammond as a refined version of the original Push, instead of manual copy/paste by dragging and dropping the hosting URL, making the phishing flow smoother and more satisfying.
ConsentFix v3 preserves the core idea of exploiting the OAuth2 authorization code flow and targeting first-party Microsoft applications that are pre-trusted and pre-authorized.
However, it brings improvements by combining automation and measurement.
ConsentFix v3 attack flow
According to information obtained from hacker forums where the new method is being developed, the attack starts by verifying the presence of Azure on the target environment by looking for valid tenant IDs.
This is followed by collecting employee information such as names, roles, and email addresses to support impersonation.
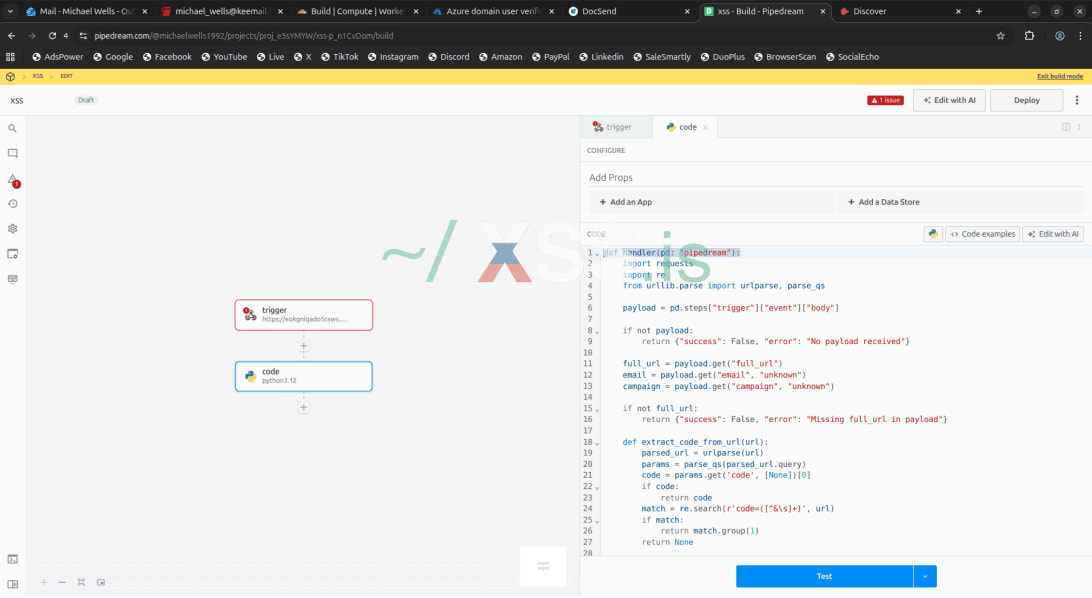
Next, attackers create multiple accounts across services such as Outlook, Ttanota, Cloudflare, DocSend, Hunter.io, and Pipedream to support phishing, hosting, data collection, and filtering operations.
Push Security researchers explain that Pipedream, a free serverless integration platform, plays a key role in automating attacks, serving three key roles:
- Is the webhook endpoint that receives the victim’s authorization code
- It’s an automation engine that quickly replaces that code with a refresh token via Microsoft’s API
- It is a central aggregator that makes the captured tokens available to us in real time.
Source: Push Security
In the next step, the attacker uses a phishing page hosted on Cloudflare Pages that mimics the official Microsoft/Azure interface and initiates a real OAuth flow to the Microsoft login endpoint.
When the victim interacts with the page, they are redirected to a host URL containing an OAuth authorization code, which they are tricked into pasting or pulling back to the phishing page.
This enables a data filtering pipeline, where the page sends the captured URL to the Pipedream web, and the backend automation quickly changes the authorization code of the tokens.
Phishing emails can be highly personalized, generated from collected data, and include malicious links embedded within a PDF hosted on DocSend to improve credibility and bypass spam filtering.
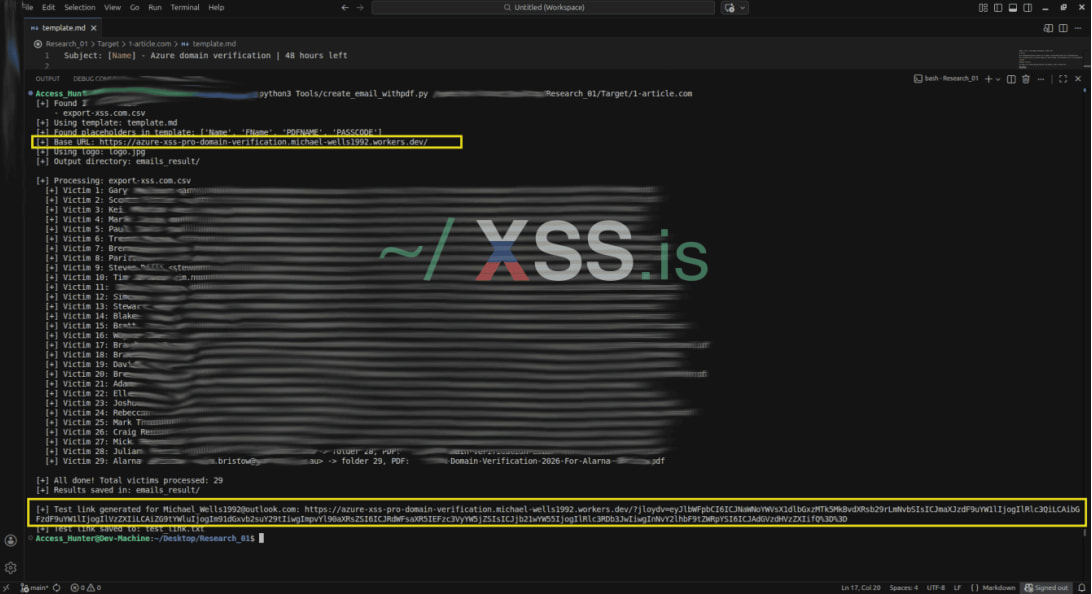
Source: Push Security
In the post-exploitation phase, the received tokens are imported into the Specter Portal, allowing the attacker to interact with vulnerable Microsoft environments and access the resources allowed by the token, such as email, files, and other resources tied to the account.
Push Security noted that its testing of ConsentFix v3 relies on its Microsoft accounts; as a result, it is difficult to fully appreciate the impact, which depends on permissions, services, and employer settings, among other factors.
In terms of reducing the risk of ConsentFix, Push notes that the effort is complicated because trusting first-party applications is by design, and that the Family of Client ID (FOCI), Microsoft applications that share permissions and refresh tokens, is useful otherwise.
However, there are still steps administrators can take, such as implementing token binding on trusted devices, setting behavioral discovery rules, and implementing application authentication restrictions.
Although the ConsentFix attack is being used in actual campaigns, it is unclear whether the v3 variant has gained traction among cybercriminals yet.

AI has tied four zero days to a single exploit that bypasses both renderer and OS sandboxes. A wave of new exploits is coming.
At the Automated Validation Conference (May 12 & 14), see how autonomous, context-rich validation finds usability, validates controls, and closes the correction loop.
Find Your Place



