Russian hackers turned the Kazuar backdoor into a modem P2P botnet

Russian hacking group Secret Blizzard has developed the long-running Kazuar backdoor into a modular peer-to-peer (P2P) botnet designed for long-term persistence, stealth, and data collection.
Secret Blizzard, whose work spans Turla, Uroburos, and Venomous Bear, has been linked to the Russian intelligence service (FSB) and is known to target government and diplomatic agencies, defense agencies, and sensitive programs across Europe, Asia, and Ukraine.
The Kazuar malware has been documented since 2017, and researchers found that its code list goes back to 2005. Its work is linked to the Turla spy group working for the FSB.
In 2020, researchers revealed its deployment in attacks against European government organizations. Three years later, it appeared to be sent to the invasion of Ukraine.
“Leader” Kazuar
Microsoft researchers analyzed the latest variant of Kazuar and observed that the malware now operates using three different modules: a kernel, a bridge, and a worker.
The Kernel module is a central coordinator that manages operations, controls other modules, elects a leader, and organizes communication and data flow throughout the botnet.
A leader is essentially a single infected system within a vulnerable environment or network segment, which communicates with a command-and-control (C2) server, receives operations, and passes them on to other infected systems.
Non-leader systems go into “silent” mode and do not communicate directly with C2. This results in better stealth and a reduced detection area.
“The Kernel Leader is the designated Kernel module that communicates with the Bridge module on behalf of other Kernel modules, reducing visibility by avoiding large amounts of external traffic from multiple infected hosts,” explains Microsoft.
The leader selection process is internal and independent, using downtime, restart, and interruption statistics.
The bridge module acts as an external communication proxy that forwards traffic between the selected Kernel leader and the remote C2 infrastructure using protocols such as HTTP, WebSockets, or Exchange Web Services (EWS).
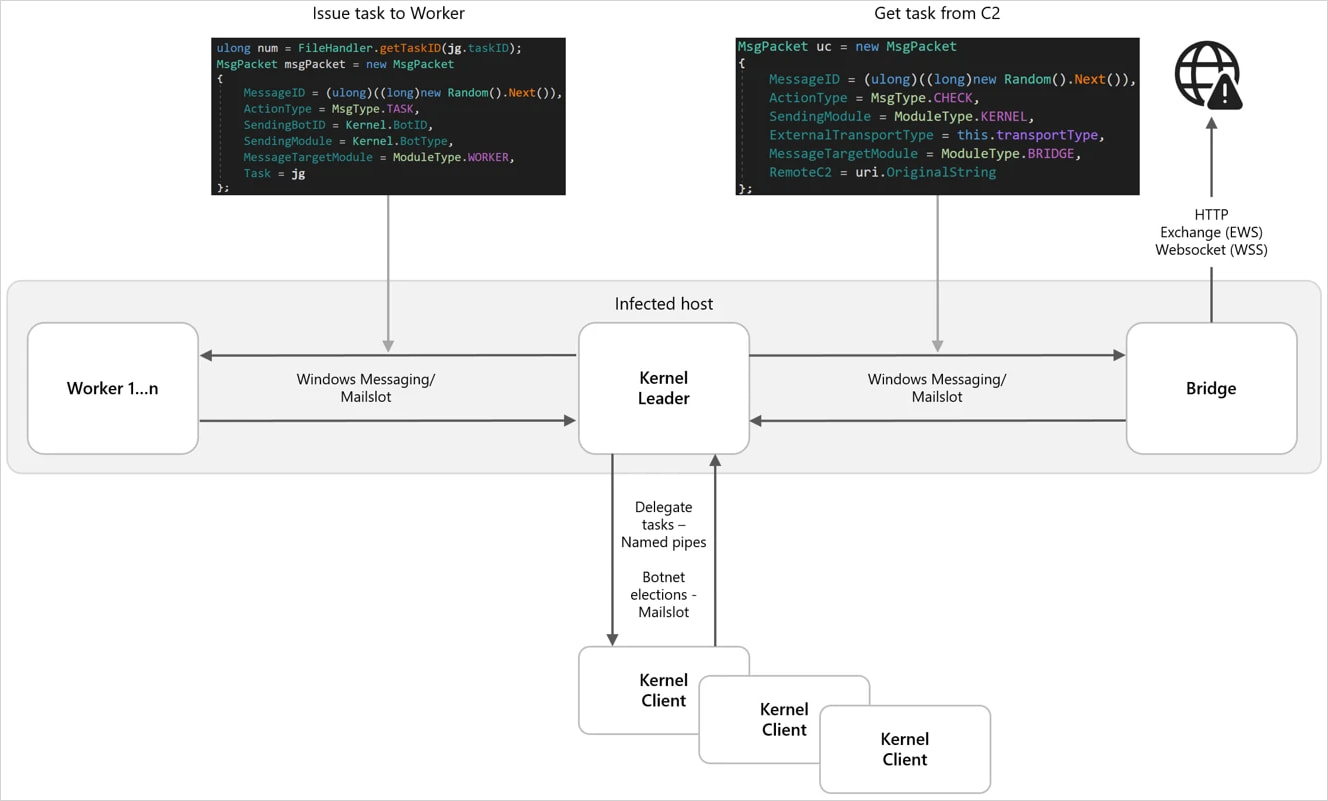
Source: Microsoft
Internal communication relies on IPC (inter-process communication), including Windows Messaging, Mailslots, and named pipes, which blend well with general operating noise. Messages are encrypted with AES and encrypted with Google Protocol Buffers (Protobuf).
The Worker module performs the actual spying tasks, such as:
- keylogging
- taking screenshots
- harvesting data from the file system
- system and network performance
- collect email/MAPI data (including Outlook downloads)
- monitor windows
- stealing recent files
The collected data is encrypted, staged locally, and later released through the Bridge module.
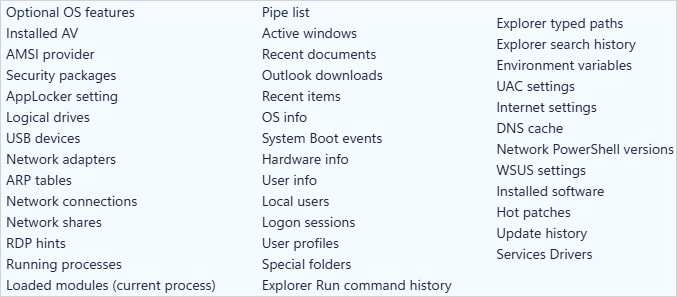
Source: Microsoft
Microsoft emphasizes the flexibility of Kazuar, which now supports 150 configuration options that allow operators to enable/disable certain security bypasses, perform job scheduling, data theft time and size of refining components, process injection, task management and command execution, and more.
In terms of security bypass options, Kazuar now offers Antimalware Scan Interface (AMSI) bypass, Windows Event Tracing (ETW) bypass, and Windows Lockdown Policy (WLDP) bypass.
Secret Blizzard often requires long-term persistence in targeted intelligence-gathering programs. The actor releases texts and email content with political significance.
Microsoft recommends that companies focus their defenses on detecting behavior instead of static signatures, as Kazuar’s programmable and highly configurable nature makes the threat evasive.

Automated testing tools deliver real value, but they’re designed to answer one question: can an attacker deploy on a network? They are not designed to check that your controls are blocking threats, your firewall detection, or your cloud configs.
This guide covers the 6 areas you really need to verify.
Download Now



